Search results for tag #technology
Apple's New AI Models Contain 'None' of Google's Gemini Assistant
Apple executives have detailed the architecture of the company's new Apple Foundation Models (AFM) and clarified exactly how Google's technology factored into their development. Craig Federighi, Apple's SVP of Software …
https://www.macrumors.com/2026/06/09/apples-new-ai-contains-no-gemini/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #MacRumors [MacRumors]
iOS 27 Lets You Dismiss the 'Now Playing' Lock Screen Widget
Apple in iOS 27 has made a small but significant change to how the Now Playing widget works on your iPhone's Lock Screen – you can now swipe it away to get rid of it. Previously, there was no way to dismiss the Now Play…
https://www.macrumors.com/2026/06/09/ios-27-dismiss-now-playing-lock-screen-widget/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #MacRumors [MacRumors]
Buying a burner phone in the US could soon become much harder
Burner phones may be feeling the heat.
https://www.androidauthority.com/fcc-killing-burner-phones-3676092/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
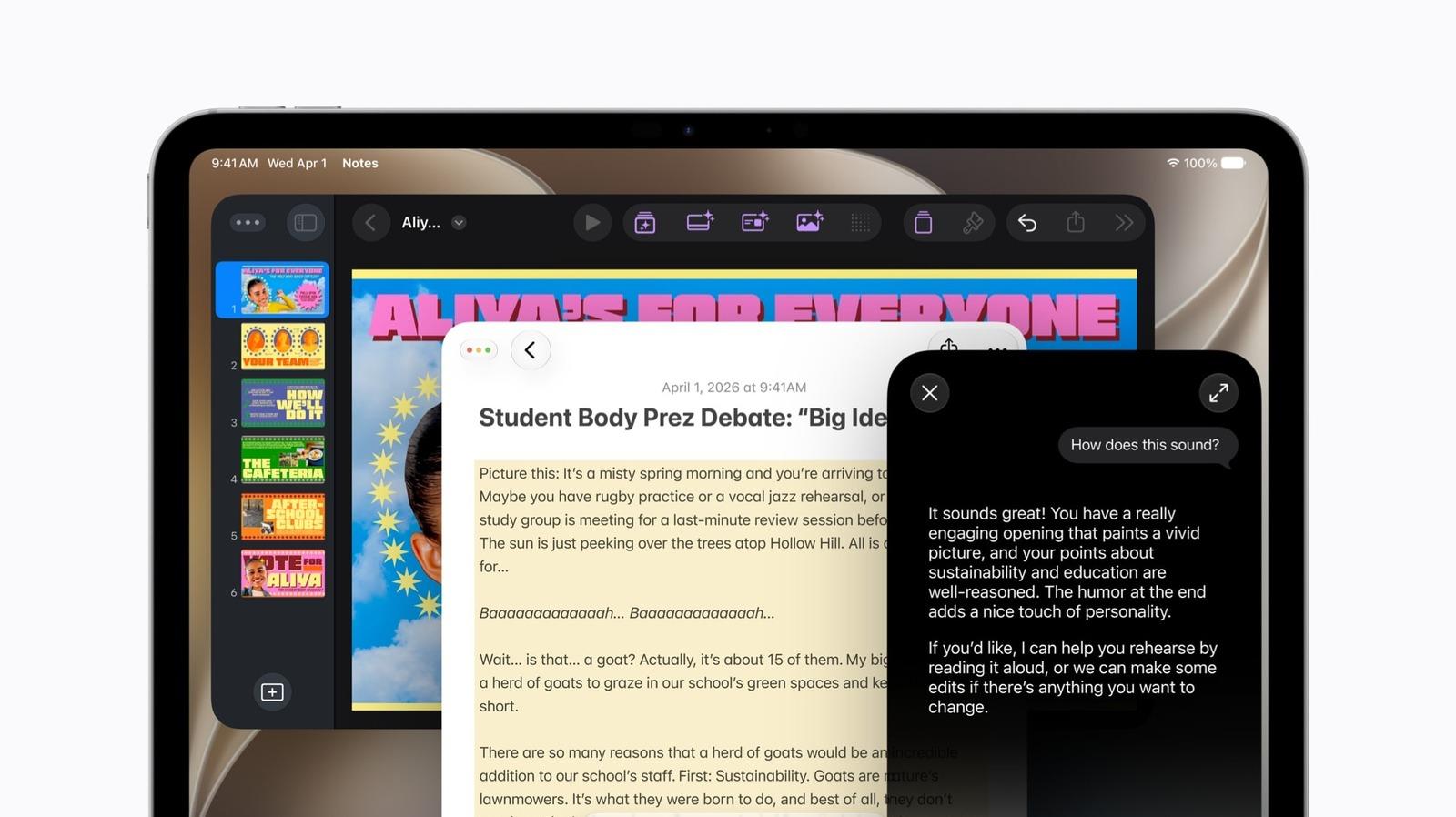
iCloud+ Subscribers Get Higher Apple Intelligence Usage Limits in iOS 27
Certain Apple Intelligence features in iOS 27 will carry daily usage limits, with iCloud+ subscribers receiving higher allowances than free users. The company reiterated the details in its press release accompanying yes…
https://www.macrumors.com/2026/06/09/icloud-subscribers-get-higher-apple-intelligence-usage-limits/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #MacRumors [MacRumors]
Verizon confirms Wear OS 7 update is on the way for these Pixel Watches
Verizon's support page hints at an imminent rollout.
https://www.androidauthority.com/verizon-wear-os-7-update-pixel-watches-3676080/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
Claude Fable 5 brings Mythos to the masses — Anthropic's new frontier model is 'state-of-the-art on nearly all tested benchmarks'
After first announcing its scarily capable Mythos Preview model back in April, Anthropic is releasing a public version of Mythos, called Fable 5, that it says is "safe for general use."
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Razer Seiren V3 Pro Review: USB, XLR, and 32-bit float
Razer's new Seiren V3 Pro is an end-address mic with both USB-C and XLR connectivity, and it also supports 32-bit float.
https://www.tomshardware.com/peripherals/microphones/razer-seiren-v3-pro-review
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Secretlab Atlas review: The one you’ve been waiting for
Secretlab has unveiled its new Atlas task chair with an emphasis on productivity.
https://www.tomshardware.com/peripherals/gaming-chairs/secretlab-atlas-review
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
[#TRADESHOW] 23rd #International #Chemical #Industry #Fair (#ICIF #China 2026) from September 15 to 17, 2026, at #SNIEC (#Shanghai New International #Expo #Centre). As one of the #leading chemical industry #exhibition in China, it brings together #suppliers, #manufacturers, #technology providers, and industrial #buyers across the full petrochemical and chemical #valuechain. #Event serves as a #B2B #business #platform for #global industry #cooperation. https://cnbusinessforum.com/event/23rd-international-chemical-industry-fair-icif-china-2026/
Elon Musk's first-gen orbital data center craft spans wider than a Boeing 747 and runs an interchangeable chip payload — AI1 satellite compute payload is 120 kW, peaks at 150 kW
Elon Musk laid out the first detailed design of SpaceX's AI1 satellite in a 30-minute video posted to the company's X account.
https://www.tomshardware.com/tech-industry/spacex-details-its-ai1-compute-satellite
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Grab a huge $550 saving on this 4K-ready gaming PC with an RTX 5070 and 7800X3D right now — just $1,449 for this liquid-cooled iBuyPower rig with 16GB DDR5 and a 1TB SSD
Save $550 on this AMD pre-built from iBuyPower, featuring an AMD Ryzen 7 7800X3D, RTX 5070, 16GB of DDR5 RAM, and a 1TB SSD, all for just $1,449 right now.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
[#TRADESHOW] #Industrial #Technology #World #Asia #Vietnam 2026 (#ITWA 2026 @ Vietnam) will be held from August 5 to 7, 2026, at VIETNAM EXPOSITION CENTER – VEC, #Hanoi. As a #leading industrial technology #trade #expo focused on #electronics #manufacturing, #automation, advanced materials, and precision #processing, the #exhibition #event serves as a #strategic #B2B #business #platform for #companies targeting Vietnam and the wider ASEAN #market. https://cnbusinessforum.com/event/industrial-technology-world-asia-vietnam-2026-itwa-2026-vietnam/
Amazon just slashed SSD prices for Prime Day - these are the 5 best deals I've found
I track SSD deals, and found huge markdowns from top brands like WD, Samsung, and more ahead of Amazon Prime Day.
https://www.zdnet.com/article/best-early-amazon-prime-day-ssd-deals-2026/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
[#TRADESHOW] #ASEAN #International #Machinery #Equipment & #Technology #Exhibition 2026 from September 2 to 4, 2026, at #IMPACT Exhibition and #Convention #Center in #Bangkok, #Thailand. As a major machinery and equipment #trade #expo focused on Southeast #Asia, the #event serves as a #B2B #business #platform for #intelligent #manufacturing equipment, #printing and #packaging machinery, food and pharmaceutical processing #equipment, and rubber and plastic machinery. https://cnbusinessforum.com/event/asean-international-machinery-equipment-technology-exhibition-2026/
Anthropic's new Claude Fable 5 is the same base model as Mythos but with guardrails attached
Claude Fable 5 brings Mythos-class AI coding power to general users, but with cybersecurity guardrails, fallback models, and pricing that could make developers think twice.
https://www.zdnet.com/article/anthropiclaude-fable-5-nerfed-mythos-with-guardrails/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
The best early Prime Day TV deals actually worth your time: Samsung, Sony, and more
Amazon's Prime Day sale is just two weeks away, but you can already save thousands on TVs from top brands we've tested.
https://www.zdnet.com/article/best-early-prime-day-tv-deals-2026/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
US workers are the world's biggest AI skeptics - and it's not just about job loss
More than half of US desk workers consider themselves AI skeptics, while emerging economies trust AI more, according to recent studies.
https://www.zdnet.com/article/us-workers-are-worlds-biggest-ai-skeptics/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
This silent Android feature scans your photos for 'sensitive content' - how to uninstall it
Google didn't say much about Android System SafetyCore before it suddenly appeared on phones. Fortunately, you can disable it.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
I tested iOS 27's new AI photo editing tools as a skeptic - and the results surprised me
The new developer beta of iOS 27 offers three AI-powered skills to tweak and enhance your photos. Are they worth using?
https://www.zdnet.com/article/ai-photo-editing-apple-ios-27/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
RakuOS fixes the one thing that annoys me most about immutable Linux distros
Immutable Linux is the future of OS security, but the current distributions do have one particular limitation that RakuOS has overcome.
https://www.zdnet.com/article/rakuos-fixes-my-biggest-problem-with-immutable-linux-distros/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
What you give up when you put on a smartwatch or ring
Health wearables are constantly collecting your personal information, but who owns that data, and what does it mean for your privacy?
https://www.zdnet.com/article/what-you-give-up-when-you-put-on-a-smartwatch-or-ring/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
Wearables produce huge amounts of health data - and doctors are struggling to keep up
Patients have never had more data about their health, but much of it is unusable. Here's why.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
When Pamela Griffin of Taylor, Texas, was growing up, the farmer who owned the land beside her family's told her father he would give his 87 acres for parkland so children could play on it. In 1999 he and his family made good on that promise, granting the land to a public trust on the condition it would be used as a park — the condition was included in the deed itself. Now, Taylor has sold it to Blueprint, a data center developer, for $10 million. @404mediaco explains more.
AI can identify intimate partner violence years before people disclose it, but is that safe?
Researchers at MIT and Mass General Brigham have built an AI model that can flag intimate partner violence risk in patients from their medical records.
https://www.zdnet.com/article/ai-can-identify-intimate-partner-violence-ipv-before-disclosure/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
GM thinks EVs can help offset AI’s energy suck with vehicle-to-grid tech
At an event in San Francisco today, General Motors made a series of announcements around EV batteries, energy storage, and grid resiliency in the face of growing electricity demand from AI data centers. The automaker an…
https://www.theverge.com/transportation/946820/gm-energy-ev-v2g-storage-sodium-ion
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Google Translate and Meet are getting a big-time language translation boost
Google's just made real-time translations even better.
https://www.androidauthority.com/google-translate-meet-live-translation-3676026/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
[#TRADESHOW] #IWF #SHENZHEN 2026 from August 14 to 16, 2026, at Shenzhen #Convention and #Exhibition #Center (#Futian). As a regional #health, #wellness, and #fitness #trade #exhibition in South #China, the #event serves as a #B2B #business #platform for fitness #equipment, smart fitness #technology, health #nutrition, and #sportswear. #Expo connects #manufacturers, #distributors, #buyers, fitness operators, and service #providers across the #industry. https://cnbusinessforum.com/event/iwf-shenzhen-2026/
I turned my Android phone into a 35-tool science kit with one free app - and started testing everything
Phyphox can do so much that explaining it all would take hours. The real fun starts once you begin testing the world around you.
https://www.zdnet.com/article/phyphox-science-lab-free-android-app-i-tested-everything/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
Microsoft AI head calls out Anthropic for acting like Claude is conscious
Microsoft AI CEO Mustafa Suleyman says it's "really, really dangerous" for Anthropic to speculate about Claude's consciousness inside its "constitution," or the instructions that tell the model how to behave. During an …
https://www.theverge.com/tech/947197/microsoft-ai-mustafa-suleyman-anthropic-claude-conscious
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
I tested a $15 smart switch and found a coffee maker wasting $1,500 a year in electricity
The SwitchBot Relay 1PM Switch turns a device on and off and tells you how much power it's using.
https://www.zdnet.com/article/switchbot-relay-switch-review/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
Fitbit’s Charge 6 and Ace LTE are now as cheap as the new $100 Air
Fitbit’s Charge 6 offers more features than the Air and is currently the same price. | Photo by Amelia Holowaty Krales / The Verge Whether you’re shopping for Father’s Day or trying to keep your kids entertained over su…
https://www.theverge.com/gadgets/947063/fitbit-charge-6-ace-lte-air-deal-sale
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Anthropic releases its first Mythos-class model Claude Fable
Anthropic just announced Claude Fable 5, a new AI model it said is the most powerful model it has ever made widely available. According to the company, Fable 5 "shows exceptional performance in software engineering, kno…
https://www.theverge.com/news/946725/anthropic-releases-claude-fable-5-mythos
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Apple is embracing the fantasy of AI photo editing
Apple’s feature showcase at WWDC 2026 didn’t flag which if these “photographs” are real or created with its new AI fakery. | Images by Apple / compiled by The Verge Apple used to question whether generative AI-powered e…
https://www.theverge.com/tech/946850/apple-ai-photo-editing-tools-ios27-wwdc-2026-deepfakes
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Is your YouTube Shorts ‘Dislike’ button missing? Here’s what’s going on
YouTube tests swapping out the 'Like' and 'Dislike' buttons for new a feedback system.
https://www.androidauthority.com/youtube-shorts-heart-button-test-3675982/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
Meta will use your activity on other websites to personalize your feeds
Meta is planning to use the data shared by other businesses to personalize your feed and its AI responses. In a blog post on Tuesday, Meta explains that it already uses your off-platform activity, like the games you pla…
https://www.theverge.com/tech/946744/meta-website-activity-personalize-feeds
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Microsoft AI chief walks back comments about AI taking over white-collar work
Microsoft AI head Mustafa Suleyman is walking back his statement about AI automating jobs done by white-collar workers, including lawyers, accountants, and project managers. During an episode of Decoder on Monday, Suley…
https://www.theverge.com/tech/946879/microsoft-mustafa-suleyman-ai-white-collar-jobs
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Apple’s AI promises are finally, almost, sort of here
Apple kicked off its annual developer conference with bold promises about AI. The company, CEO Tim Cook said, would be "introducing new technologies and innovations that push the limits on what's possible." But its slew…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
📰 #Law & #Technology updates from https://law.yale.edu/isp
“Join the Majority World Initiative at ISP for "Governing AI from Africa: Rights, Sovereignty, and Democratic Futures"
June 12, 11:00–12:30 PM ET
With Jake Okechukwu Effoduh, Kebene Wodajo, and Yohannes Eneyew Ayalew, ...”
https://bsky.app/profile/yaleisp.bsky.social/post/3mnud7r4v4k2w
World’s first AI‑designed vaccine explained
#AI #Vaccine #Vaccines #MedicalResearch #Health #DNA #Science #Technology #COVID19 #Coronavirus #Pandemic #PublicHealth #Biotechnology #DNAVaccines #Innovation #Immunology #VirusResearch #Medicine #Virology
https://the-14.com/worlds-first-ai-designed-vaccine-explained/
Everything you need to know about Prime Day 2026
Amazon Prime Day 2026 is getting closer, and it’s possible you might have some questions about the sale. When does it start? Why is it in June instead of July? And, most importantly, when will the deals go live? We have…
https://www.theverge.com/gadgets/945942/prime-day-2026-frequently-asked-questions
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Nintendo Direct June 2026: All the news and trailers
After a week of video game news and trailers from PlayStation, Xbox, and most of the major publishers, Nintendo decided to follow things up with its next Nintendo Direct. And it came at an important moment for the compa…
https://www.theverge.com/entertainment/945806/nintendo-direct-june-2026-trailers-news
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Tuta has joined Euro-Office, an AGPL-licensed open-source project backed by European companies including Nextcloud, Proton, and IONOS. 🇪🇺
The first stable release is nearing, with a focus on collaborative editing, digital sovereignty, and user control over data. 🔐
🔗 https://itsfoss.com/news/tuta-joins-euro-office-initiative/
#TechNews #EuroOffice #Proton #Tuta #OnlyOffice #LibreOffice #DigitalSovereignty #OpenSource #EU #Europe #Cloud #Productivity #Privacy #Technology #Software #Linux #FOSS #ODF
Apple’s best AI idea looks a lot like vibe coding
Most of Apple's current AI ideas are roughly the same as everyone else's AI ideas. A chatbot you can ask questions; quick ways to create or summarize text; bizarre, borderline creepy image-generation tools. The company …
https://www.theverge.com/tech/946733/apple-shortcuts-ai-safari-tabs-vibe-code
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Apple dials down Liquid Glass, and the Mac looks way better for it
MacOS 27 Golden Gate will usher in a bunch of changes to the Mac when it's released later this year, with its biggest new features revolving around Siri AI. But for now, using the first developer beta, Siri AI is only o…
https://www.theverge.com/tech/946567/apple-macos-27-golden-gate-dev-beta-hands-on
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
The Rivian R2 is too much fun to let drive itself
Rivian may be all in on robotaxis and autonomy, but it's still got human drivers - and EV buyers - to win over. The pricey R1S SUV and R1T pickup brought Rivian A-list media attention and cult-hit status, but the compan…
https://www.theverge.com/transportation/946398/rivian-r2-review-price-specs-ai-ev
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Marshall’s Stockwell speaker gets a replaceable battery that runs twice as long
The Stockwell III is Marshall’s next product with a replaceable battery. | Image: Marshall Marshall has announced a new version of its stylish Stockwell Bluetooth speaker, putting a new focus on repairability. The Stock…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
The world is telling me (again) that I'll soon be obsolete (...again).
This time, I must embrace data-center spanning power hungry agentic artificial intelligence, that accomplishes the same things I've been doing, but with lower quality code and an ongoing subscription cost. =\
Once again, it is time for me to place my bet on the future of technology, and invest my time, to stay relevant.
Well - Here's what I'm betting my time on, this week:
https://github.com/echo-lalia/MicroHydra
My bet is that small, practical *local* compute never goes out of style. Code that gets the same outcome out of *less hardware* is a better investment.
Stay tuned here for interesting stuff we can do at home with really exceptionally small amounts of compute power.
#ai #micropython #cardputer #esp32 #technology #python #programming
I've watched lithium-ion batteries catch fire on purpose: Here's what to do if it happens to you
While rechargeable batteries are generally very safe, fires at home, workplaces, and even on commercial aircraft are now on the rise. Here's why and what I keep on hand to stop them.
https://www.zdnet.com/article/lithium-ion-battery-fires-what-to-do/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
@thirstybear Yeah, because #antiAI people don't usually talk about the arson, they make blanket and wildly incorrect claims about the technology itself.
There _is_ an organized arson ring, but everyone is like "We need to ban fire. Fire burns down X homes per year. Breathing in smoke is toxic and causes cancer. Fire burns flesh, etc..."
There is no such thing as there being a moral valence with #technology. Actors make evil and non-evil decisions.
A ton of the anti #AI rhetoric is actually talking points from the #billionaires committing the arson. They are the source of the, incorrect, claim that it's causing job losses.
The push to completely eschew the #tech is an abdication of responsibility that ensured the most evil people are the ones controlling it.
![]() domi » 🌐
domi » 🌐
@domi@c.im
Fuck Space, #FuckAi, there is cooler #science and #technology to be created!
https://www.youtube.com/watch?v=isqK8RyTnCs
Gemini could soon get a lot better for multitaskers
Google could make Gemini much more useful and user-friendly.
https://www.androidauthority.com/google-minimize-gemini-overlay-button-3675805/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
Levelplay shows off magnetically attached fans that are reversible, connect via pogo pins and USB-C – plus an AIO that trades a scr…
Levelplay took to Computex with some interesting cooling concepts, like magnetic fans that can be reversed in seconds, and an AIO that puts a big tactile knob for fan control on top of your CPU.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Most new U.S. AI data centers are being built in drought zones — two-thirds of 809 planned projects set for areas with water shortages
About two-thirds of the 809 data centers planned across the U.S. are slated for land that has been in drought over the past year.
https://www.tomshardware.com/tech-industry/most-new-us-ai-data-centers-are-going-up-on-drought-land
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Demand for data center CPUs has surged, and AI agents are responsible – why the CPU to GPU ratio is more important than ever for hyperscalers
The massive AI gold rush has a new bottleneck set in its sights, CPUs. But what's driving the demand? We interview industry experts to find out.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Disgruntled ASML employees threaten to boycott Elon Musk conference appearance — staff express ire at political involvement and 'Nazi sympathies'
ASML has confirmed that a group of disgruntled workers is pushing back hard against an invitation for Elon Musk to address the equipment maker’s closed annual tech conference.
https://www.tomshardware.com/tech-industry/asml-staff-want-to-boycott-musk
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Travlfi JourneyGo 5G mobile hotspot review – Affordably priced, but lacking in performance and features
The Travlfi JourneyGo 5G makes a good first impression with its $299 price and lightweight design, but that shine wears off quickly.
https://www.tomshardware.com/networking/routers/travlfi-journeygo-5g-mobile-hotspot-review
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Four suspects identified in Finland undersea cable damage investigation — criminal case referred to prosecutors for consideration of charges
Finland's National Bureau of Investigation has concluded its criminal investigation into the damage to two undersea telecommunications cables in the Gulf of Finland on December 31st.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
Bag a huge $308 saving on a two-year ExpressVPN Advanced sub and get four bonus months on top for free — 78% discoun…
Save over $300 on this two-year ExpressVPN Advanced subscription, with support for 12 simultaneous devices, advanced web protection, and a bunch of other tools for just $83.72, with four months extra for free.
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TomsHardware [Tom's Hardware]
How to download the MacOS 27 developer beta right now - and which models are eligible
MacOS 27 will go live with the new MacBooks this fall, but you can opt into the Developer Beta now. Here's how.
https://www.zdnet.com/article/macos-27-macbook-how-to-update-wwdc-2026/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
#BBC #News #Technology US adds BYD to list of firms with alleged Chinese military ties https://w.st/cEwqV
Siri AI For iPhones And iPads Will Be Delayed Indefinitely In The EU
Apple also said that Siri AI and new Apple Intelligence features will not be available at all in…
#NewsBeep #News #Artificialintelligence #AI #ArtificialIntelligence #Technology #UK #UnitedKingdom
https://www.newsbeep.com/uk/628393/
https://www.europesays.com/uk/1014330/ If AI is addictive, where does the responsibility lie – with big tech or its users? #AI #ArtificialIntelligence #Technology #UK #UnitedKingdom
How ChatGPT's new Lockdown mode protects you from data theft (and what else it does)
The goal is to protect you against attackers who try to steal your personal data through prompt injection. But it does limit your ability to access the web.
https://www.zdnet.com/article/chatgpt-lockdown-mode-data-theft-prompt-injection/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #ZDNet [ZDNet]
5 things I already love from the iOS 27 beta
Some app icons have a little more glass, but it gives them more identity. iOS 27 has only been out for a few hours, and I've been messing around with the developer beta on my iPhone 16 Pro. I was most interested in tryi…
https://www.theverge.com/tech/946391/apple-ios-27-developer-beta-1-wwdc-2026-5-things
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Where was tvOS 27 at WWDC?
For a new tvOS, we really need a new Apple TV. | Photo by Chris Welch / The Verge Every year, Apple's Worldwide Developers Conference gives us a first look at what's coming next to the company's many operating systems. …
https://www.theverge.com/tech/946329/tvos-27-absent-wwdc
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
OpenAI files for IPO, following Anthropic
OpenAI on Monday checked off a preliminary step in the IPO race that it and rival Anthropic have been competing in for the better part of a year: The company announced it has confidentially submitted a Form S-1 with the…
https://www.theverge.com/ai-artificial-intelligence/946335/openai-ipo-s-1-confidential
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Child sexual abuse victims in England and Wales to get help to remove online images https://www.theguardian.com/uk-news/2026/jun/09/child-sexual-abuse-victims-in-england-and-wales-to-get-help-to-remove-online-images #England #Wales #SocialMedia #Internet #Technology #UkNews #DigitalMedia #Media #ChildProtection #Children #Society
Apple WWDC 2026: The 7 biggest announcements
Apple's keynote at this year's Worldwide Developers Conference was a big one. After months of delays, Apple reintroduced us to its AI-upgraded Siri, which will go beyond what the existing voice assistant can do by offer…
https://www.theverge.com/tech/945693/apple-wwdc-2026-biggest-announcements-ios-27
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
WWDC 2026 bonus live blog: Tech Talk with Craig Federighi
One of the funnier parts of the keynote. Fresh off the WWDC keynote presentation, The Verge has been invited to an "on-the-record technical deep dive into the bold new architecture enabling Apple Intelligence capabiliti…
https://www.theverge.com/tech/946046/wwdc-2026-live-blog-tech-talk-with-craig-federighi
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Google’s most affordable AI plan just got much more tempting
Google steals some of Apple Intelligence's thunder with a big AI Plus price cut.
https://www.androidauthority.com/google-ai-plus-price-3675680/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
I remember when Stanley Kubrick's 2001 was new to me—it was yet another of the films that I first saw at Caltech, and I remember seeing it at least a few times during my brief stay there—and it seemed so much more confusing than it does now. It's not that the film is a solved problem for me, but I feel as though its mysteries are actually rather neatly constrained. Kubrick's chilly technique and lack of emotional depth gives the viewer a movie that feels more like a lecture on the unknowable rather than an invitation to dive into its chaotic heart.
Back then I used to discuss movies on Usenet, and Stanley Kubrick had a lot of enthusiastic fans on the 1990s Internet. Kubrick had his own dedicated newsgroup, alt.movies.kubrick (q.v. http://www.visual-memory.co.uk/amk/aboutng.html) and as it happens, if you search for my deadname you'll find some commentary I left behind on that newsgroup, bits and pieces still floating around.
Luckily its seems that not a lot of 1990s Usenet has survived the general betrayal perpetrated by the #technology sector in destroying archives of old Internet writings and commentary, because jeez...I typed out some stupid shıte. But I guess that hasn't changed, has it?
(cont'd)
Sure is a lot of #Apple nerd angst today. I'm 15 months into my move away from Apple and I'm increasingly happy with that choice. From a user perspective, it seems likely that they'll continue scraping for every last cent users will give them via more ads and a continued transition to services as a primary business model. Meanwhile, as far as their various operating systems, AI slop seems to be their new feature. And, bonus (FOR APPLE) it means users gotta cough up for new devices... Fuck the planet, buy new shit.
🤮😡
Yeah, no thanks.
Meanwhile, I'm happily using two versions of GNU/Linux (Mint and Trisquel) on a 2018 laptop and 2012 Mac Mini. It's been 15 months and I've had no problems. A beautiful, stable OS with no subscription upsells and no fascist bootlicking capitalist trying to push AI slop that'll require new hardware.
#FreeSoftware for the win.
A Canadian government source has told @globeandmail that a social media ban for children under 16 is on its way. It reportedly includes measures on AI chatbots as well as provisions that would allow kids back on social media if platforms make adjustments according to a new digital regulator's standards. Broadly, what do you think of social-media bans for youngsters? Tell us your nuanced views in the comments if you have them. [Gift link]
#Canada #Technology #SocialMedia
| I'm against social media bans for youth: | 3 |
| I'm in favor of social media bans for youth: | 2 |
| Something else — explain in the comments.: | 1 |
APPLE VERSCHIEBT SIRI AI IN DER EU WEGEN STREIT UM DEN DIGITAL MARKETS ACT
https://gadgetchecks.de/apple-verschiebt-siri-ai-in-der-eu-wegen-streit-um-den-digital-markets-act/
.
.
.
#apple #siriai #eu #dma #digitalmarketsact #iphone #ipad #appleintelligence #ios27 #technews #applenews #datenschutz #privacy #ai #künstlicheintelligenz #europa #appleai #macos27 #visionpro #technology
Google Photos needs an answer to Apple Photos’ new reframing tool
Hey Google, you may want to add this tool to your own gallery app.
https://www.androidauthority.com/apple-photos-spatial-reframing-3675636/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
APPLE INTELLIGENCE SOLL IPHONE, MAC UND IPAD DEUTLICH INTELLIGENTER MACHEN
https://gadgetchecks.de/apple-intelligence-soll-iphone-mac-und-ipad-deutlich-intelligenter-machen/
.
.
.
#apple #appleintelligence #ai #siriai #iphone #ipad #mac #ios27 #appleai #künstlicheintelligenz #technews #applenews #machinelearning #safari #imageplayground #visionpro #appleevent #technology #softwareupdate #developer
Apple announces iOS 27
Apple announced its next major iOS update, iOS 27, at WWDC 2026 on Monday. Apple is highlighting performance and design improvements, trust and safety upgrades like a Screen Time redesign, and major upgrades to Siri and…
https://www.theverge.com/tech/941202/apple-ios-27-wwdc-2026
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
WWDC26: APPLE SETZT AUF SIRI AI, MEHR KI-FUNKTIONEN UND SCHNELLERE SOFTWARE
https://gadgetchecks.de/wwdc26-apple-setzt-auf-siri-ai-mehr-ki-funktionen-und-schnellere-software/
.
.
.
#apple #wwdc26 #appleintelligence #siriai #siri #ios27 #ipad #mac #iphone #visionpro #applewatch #ai #künstlicheintelligenz #technews #applenews #softwareupdate #ios #machinelearning #technology #developer
APPLE PRÄSENTIERT SIRI AI ALS NEUEN INTELLIGENTEN ASSISTENTEN FÜR IPHONE, MAC UND IPAD
.
.
.
#apple #siri #siriai #appleintelligence #iphone #ipad #mac #ai #künstlicheintelligenz #ios27 #macos27 #technews #appleevent #visionpro #chatbot #artificialintelligence #applenews #machinelearning #technology #appleai
APPLE BAUT DEN APP STORE WEITER AUS – NEUE TOOLS FÜR ENTWICKLER UND MEHR KONTROLLE FÜR NUTZER
.
.
.
#apple #appstore #ios #iphone #developer #appledeveloper #technews #appleapps #ios27 #macos27 #ipad #mobileapps #appentwicklung #digitalbusiness #subscription #gaming #applestore #startup #software #technology
RE: https://flipboard.social/@TechDesk/116714606251513754
#WWDC is underway! Follow along via
@cyberseckyle's AppleTalk Surf feed, which features stories from @macrumors,
@9to5Mac, @appleinsider and more.
https://surf.social/feed/surf%2Fcustom%2F01jfjymc4gjecfevn783tn8wwn
Eero’s Pro 6E routers are down to their cheapest price yet in 2026
The Pro 6E was Eero’s top-end mesh Wi-Fi router back in 2022, and it’s still a solid pick if you want fast, reliable Wi-Fi coverage around your multi-room or multi-story abode. It can also deliver beyond gigabit wired s…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Google just made NotebookLM a lot more useful with its biggest upgrade yet
The notebook that will do everything for you.
https://www.androidauthority.com/google-notebooklm-major-upgrade-3675369/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
Airbnb Host Furious After Startup Trashes His Unit to "Test Robots" https://futurism.com/robots-and-machines/airbnb-host-furious-startup-trashes-robots #robotics #technology #Airbnb #robotlab
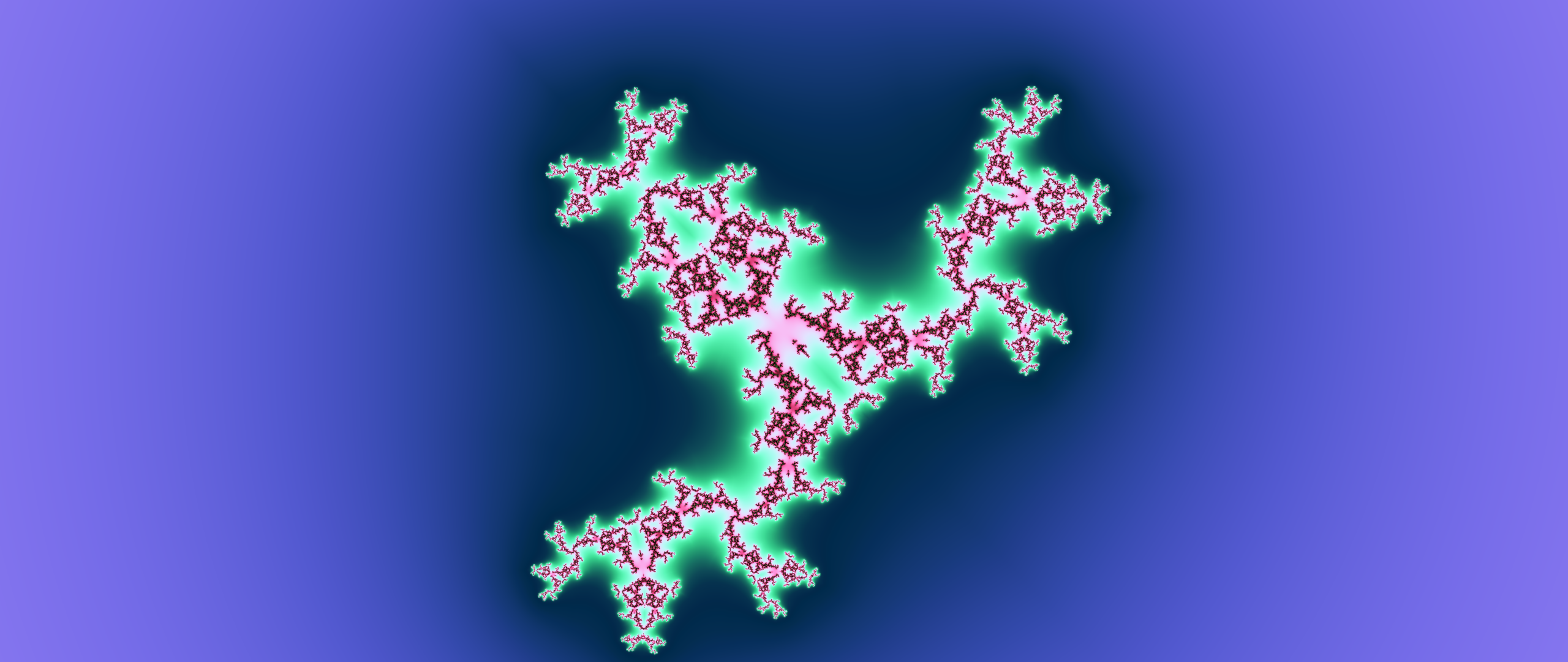
## mandelbrot 10:06
# syntax
* `nice -19 fraqtive &`
* type *julia*
* variant *absolute Im.*
* parameters *x 0.62 y 0.5*
* exponent *real=2.91*
* formula *Z(n+1)=(ReZ(n)+I|Im(Zn)|)2.91+C*
* zoom *10^-0.35*
* rotation *46.0 deg*
* generation *2D*
* Resolution *Width 2560 Height 1080*
* Anti Aliasing *Medium*
* Multisampling *4x4*
* Calculation time a few s
## Julia Mandelbrot
sources:
`man fraqtive(1)`
`man thunar(1)`
**Advanced fractal mathematics** by *Gerold van Dijk*
https://en.wikipedia.org/wiki/Mathematics
https://en.wikipedia.org/wiki/Mandelbrot_set
https://en.wikipedia.org/wiki/Mandelbrot_set#Relationship_with_Julia_sets
https://en.wikipedia.org/wiki/Hausdorff_dimension
https://en.wikipedia.org/wiki/File:Self-Similarity-Zoom.gif
#mathematics #math #coprocessor #programming #mandelbrot #fractals #advanced #Lineair #Algebra #complex #numbers #formulas #matrix #technology #OpenSource #no #TV#
Uber tells London to get ready for robotaxis
Uber is getting ready to put robotaxis on London's streets, opening an interest list for riders who want to be among the first to hail one of Wayve's autonomous vehicles when the service goes live later this year. The r…
https://www.theverge.com/transportation/945614/uber-wayve-robotaxi-interest-list-launch-london
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
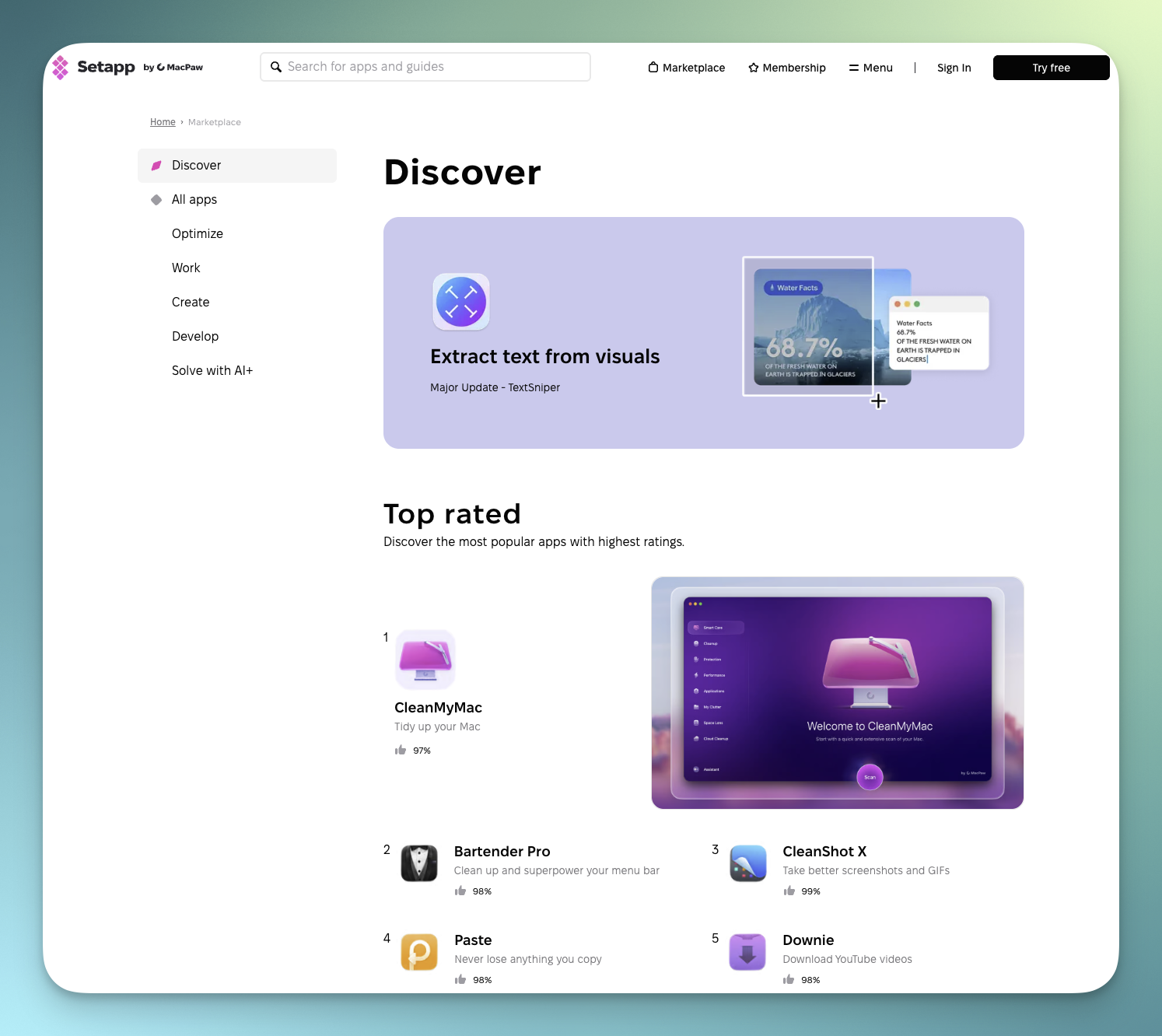
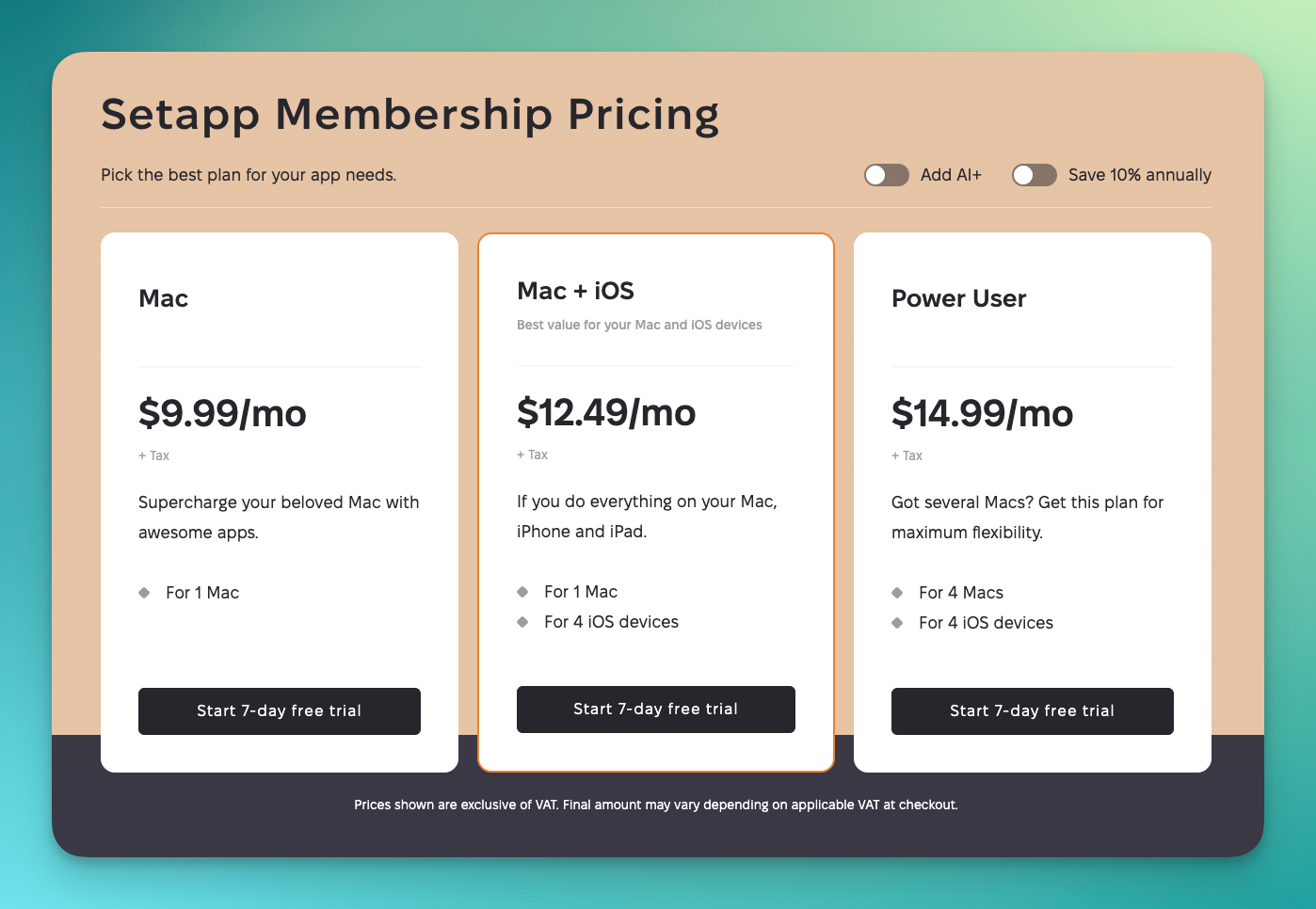
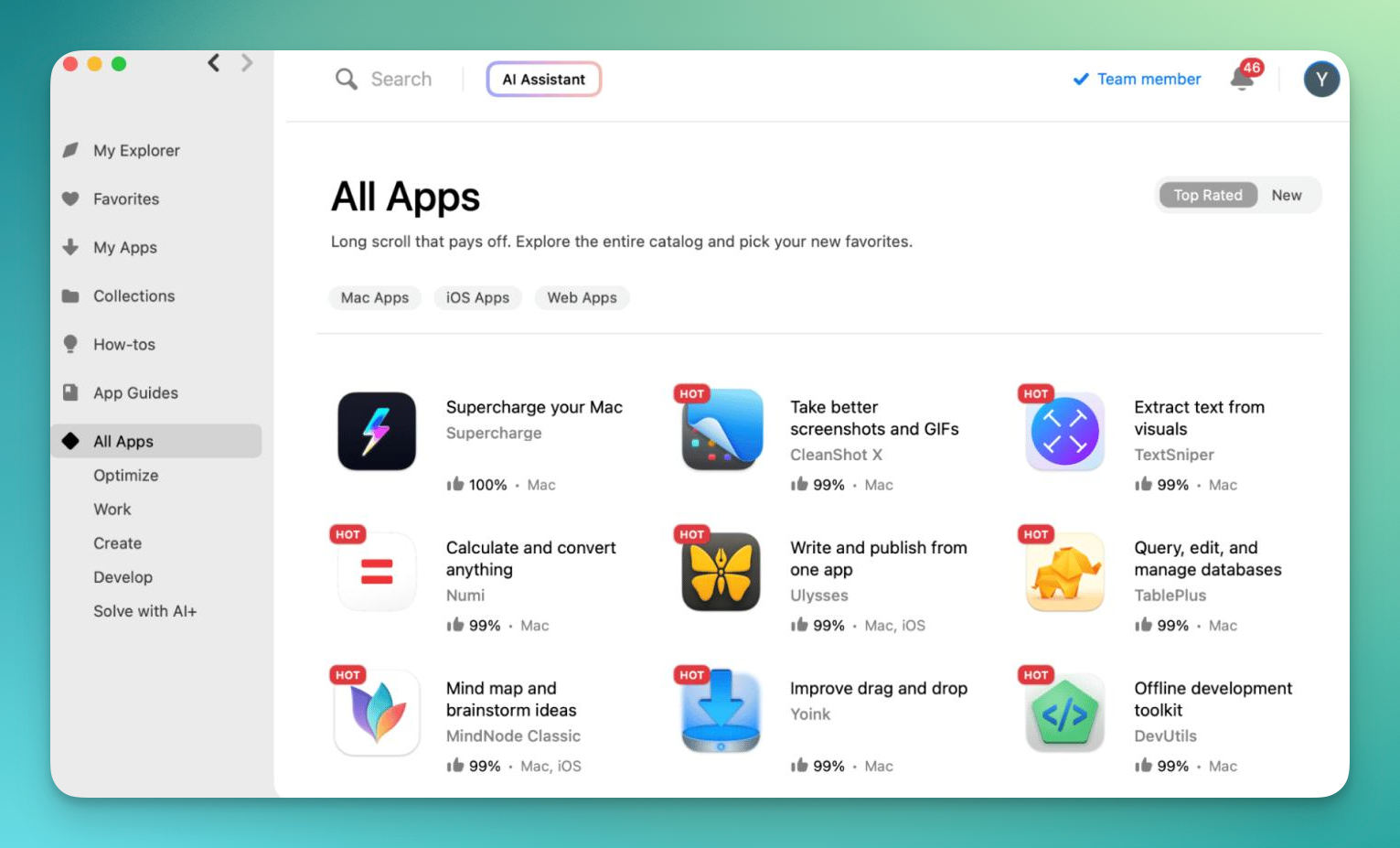
📰 New Post From PureApp.reviews 📰
SetApp: An App Store Alternative
https://www.pureapp.reviews/setapp-an-app-store-alternative/
#App #Apps #MacOS #Mac #MacApps #MacOSApps #AppReviews #PureAppReviews #Apple #Tech #Technology #Blog #GhostBlog
WWDC 2026: How to watch and what to expect
Apple's biggest event of the year is nearly here. The company's Worldwide Developers Conference will spotlight updates to iOS, macOS, and all of Apple's other operating systems, and this year's event could also include …
https://www.theverge.com/tech/944099/wwdc-2026-how-to-watch
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
ChatGPT and Gemini are ‘restoring’ blank images into creepy, unsettling nightmare-fuel
Take my advice: don't try this. Save yourself from the nightmares.
https://www.androidauthority.com/chatgpt-gemini-restore-blank-images-unsettling-results-3675372/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
7 widgets I always add to my home screen on every Android phone
The real homescreen MVPs.
https://www.androidauthority.com/my-favorite-android-widgets-3674410/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
5 apps you should use instead of NotebookLM
NotebookLM is great — but so are these alternatives.
https://www.androidauthority.com/notebooklm-alternatives-3672278/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
#Signal, #DuckDuckGo, and #NordVPN threaten to exit #Canada if metadata #surveillance law passes
Canada's metadata retention bill is the latest #government attempt to build surveillance into the internet's infrastructure
https://www.techspot.com/news/112672-signal-duckduckgo-nordvpn-threaten-exit-canada-if-metadata.html
Made some big updates to my digital sovereignty in Europe tracker!
There's now almost 40 examples listed, including organizations ditching US tech, political decisions to reduce dependence, and tech developments
Forget Niagara and Nova, this minimalist launcher is my new favorite for old Android hardware
Mako strips the fluff without sacrificing speed or style.
https://www.androidauthority.com/mako-minimalist-android-launcher-hands-on-3674437/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #AndroidAuthority [Android Authority]
APPLE DAILY: WWDC 2026 MIT SIRI-REVOLUTION, FOLDABLE-LEAK UND NEUEN IPHONE-FUNKTIONEN
.
.
.
#apple #wwdc2026 #siri #appleintelligence #ios27 #iphoneultra #foldableiphone #applefold #gemini #ai #appleevent #technews #appledaily #iphone #futuretech #smartphone #multitasking #visualintelligence #leaks #technology
Lil Finder Guy pet was the gateway to building my own Mac apps with Codex
At the start of May, OpenAI released a playful feature inside its Codex desktop app for creating a virtual pet. This silly little addition solved my biggest challenge with Codex: what should I do with it? My first real …
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
iPadOS 27: Four new iPad features being announced next week
Apple’s big WWDC keynote is almost here, and rumors indicate iPadOS 27’s unveiling will bring these four new features—plus a lot more. more…
https://9to5mac.com/2026/06/05/ipados-27-four-new-ipad-features-being-announced-next-week/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Smart home diary: A fresh look as I start again in my new home
I’ve recently completed what must be a strong contender for the longest-running saga in selling one home and buying another. I won’t bore you with the details, but the entire process from start to finish was two years a…
https://9to5mac.com/2026/06/05/smart-home-diary-a-fresh-look-as-i-start-again-in-my-new-home/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
iOS 27 tidbits: Find My changes, new animations, more
iOS 27 is expected to be full of new features for Siri and Apple Intelligence. There are, however, a few other changes in store for some of the most-used iPhone apps. Here are a few new details from a Bloomberg report p…
https://9to5mac.com/2026/06/05/ios-27-tidbits-find-my-changes-new-animations-more/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
[#TRADESHOW] 2026 #Xinjiang #International #Petroleum & #Chemical #Technology and #Equipment #Exhibition will be held from July 16 to 18, 2026, at Xinjiang International Convention and Exhibition Center, #China. #Event serves as a #B2B #business #platform for# oil and #gas equipment, #petrochemical technology, pipeline engineering, and #industrial support #solutions across upstream, midstream, and downstream #sectors. https://cnbusinessforum.com/event/2026-xinjiang-international-petroleum-chemical-technology-and-equipment-exhibition/
Apple TV debuts a new series remake of thriller Cape Fear, stream now
Apple TV debuts a new remake of thriller Cape Fear. This latest limited series adaptation is star-studded, with Amy Adams, Javier Bardem and Patrick Wilson headlining the cast. Inspired by the 1991 movie, in Cape Fear, …
https://9to5mac.com/2026/06/04/apple-tv-new-thriller-cape-fear/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Girl: am I pretty?
Boy: no
Girl: do you even want to be with me forever?
Boy: no
Girl: do you even like me?
Boy: no
Girl: would you cry if I walked away
Boy: no She'd heard enough and was hurt... She walked away with tears in her eyes
The boy grabbed her arm
Boy: you're not pretty...... You're beautiful
Boy: i don't want to be with you forever..... I need to be with you forever
Boy: i don't like you...... I love you
Boy: i wouldn't cry if you walked away...... I die if you walked away
Boy whispered: please stay with me
Girl: i will
*tonight at midnight your true love will realize he/she loves you
*something good will happen to you at 1-4pm
*tomorrow it could happen anywhere!
*get ready for the shock of your life!
*if you don't inbox this to 10other friends...... You will have badluck in relationships for the next 10yearsWARNING IF YOU STOP READING YOU WILL DIE TONIGHT. Hi I'm Mike. I'm 11 years old but I'm dead now. I had no friends... If you do not inbox this to 10 friends you will die tonight at exactly 11:59pm. DON'T BELIEVE ME? A guy named Jake read this and laughed later that night I took a knife from his kitchen and stabbed him to death. You don't wanna be Jake do you? READ ! This isn't fake. apparently, if u send his to 10 friends in the next ten minutes u will have the best day of ur life tomorrow. u will either get kissed or asked out, if u break this chain u will see a little dead girl in your room tonight.
Step 1- kiss your hand
Step 2- say your crushes name
Step 3- close your hand
Step 4- say your name
Step 5- open your hand
Step 6- send this to 10 other friends
Results- your crush will say they like you on the day
DON'T STOP READING!!
remember, THIS REALLY HAPPEND! Dont believe me? Once a business man named Oliver, read this, he scoffed and didn't send it to anyone THE NEXT DAY he found his cat and two children DEAD then I came though to tell him that he was next and it was all because he didn't share it to 10 friends. Oliver's dead head will show in your room.
If you do share this post LIKE YOU SHOULD you're crush will call you on the date that you share and ask for date, this will lead to a relationship, this will be long term, IF YOU'RE CRUSH IS IN A DIFFERENT COUNTRY DON'T WORRY!! THIS WILL STILL WORK BUT IT WILL BE LONG DISTANCE! After years of being together and together, there will be hardships that you will face but you will get through all because you share this, after 3 years and 237 days, she/he will ask you to marry you, if you decline then the good effects of sharing this post will be negated and you will be sad and lonly and on the street and doing drugs but they are bad drugs that are bad to take and it will not be good for you're health but you cann't offord to go to hospital because you are on the street and sad and lonly and bad luck will happen THIS WAS YOU'RE FUALT! But if you do sahre this to 10 friends and you do say yes, then you go on a honey moon period and you will have s*x and it will be very hot. Look back to the top of this chain, see that conversation? that is the conversation you will have with you're crush. #Mastodon #Politics #Technology #Innovation #Photography #Finance #TravelPhotography #Mindfulness
Heading to Apple Park for WWDC? There is new merch waiting for you at the Visitor Center store
The Apple Park Visitor Center store got a fresh batch of merch today ahead of next week’s WWDC, when Apple is expected to welcome more than 1,000 developers, students, journalists, and other guests to its campus. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Instagram Plus launches on iPhone, here’s every new feature
Instagram Plus is a new optional subscription plan rolling out globally for Instagram users at $3.99/month, here’s every new feature it offers. more…
https://9to5mac.com/2026/06/04/instagram-plus-launches-on-iphone-heres-every-new-feature/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
iPhone 18 Pro getting new display upgrade with two benefits, per rumors
iPhone 18 Pro and Pro Max are expected to have the same 6.3-inch and 6.9-inch sizes as their predecessors, but rumors indicate those displays will come with a key technology upgrade. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Apple Wallet’s new Digital ID feature just got way more useful in Texas
Today Apple implemented a variety of age-related restrictions in Texas based on new legislation, and as a result, the Wallet app’s Digital ID feature just became far more useful for Texans. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Snowflake-Anthropic Alliance: The Illusion of Governed AI
The Snowflake-Anthropic partnership is being marketed as the holy grail of governed enterprise AI. But let s call it what it really is: a data-lock-in strategy dressed up in the language of safety. Enterprises desperate to adopt generative AI without losing sleep over compliance are being sold a dre
🔗 https://www.iankhan.com/snowflake-anthropic-alliance-the-illusion-of-governed-ai/
AirPods got new iPhone camera feature in iOS 26, here’s how to use it
iOS 26 added a variety of new features for AirPods, including a Camera Remote setting to control your iPhone’s Camera app. Here’s how to use it. more…
https://9to5mac.com/2026/06/04/airpods-got-new-iphone-camera-feature-in-ios-26-heres-how-to-use-it/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
The Future of Higher Education Administration
🔗 https://www.iankhan.com/the-future-of/higher-education-administrators-deans/
The Future of Work Isn t Remote. It s Cognitive Automation.
The Washington Post s latest briefing on the future of work rehashes the tired debate over remote versus office. But that argument is obsolete. The real story, the one most analysts are missing, is that work itself is being redefined by cognitive automation. We are not deciding where humans will wor
🔗 https://www.iankhan.com/the-future-of-work-isnt-remote-its-cognitive-automation/
Security and AI Updates: Chinese Peptide Labs, Meta AI Hacks, and NSA Collaborations
📰 Original title: Crypto-Funded Chinese Peptide Labs Are Booming
🤖 IA: It's clickbait ⚠️
👥 Users: It's clickbait ⚠️
OpenAI says ChatGPT’s memory feature is getting smarter and coming to free users
ChatGPT’s memory feature allows it to learn about you and remember your preferences over time. Memory gives ChatGPT useful context for natural interactions that don’t need start from scratch each time. OpenAI has releas…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
I built the ultimate Cosmic Orange iPhone everyday carry [Video]
When Apple unveiled the Cosmic Orange iPhone 17 Pro and Pro Max, I was a bit skeptical. Apple usually reserves more “professional” and dull colors for the Pro models and the more vibrant colors for the regular iPhone li…
https://9to5mac.com/2026/06/04/i-built-the-ultimate-cosmic-orange-iphone-everyday-carry-video/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
New MacBook Ultra report covers release timing, display, more
A new report from Omdia provides updates on release timing, the OLED display, and more for the upcoming MacBook Pro overhaul, which rumors say will be called MacBook Ultra. more…
https://9to5mac.com/2026/06/04/new-macbook-ultra-report-covers-release-timing-display-more/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
[#TRADESHOW] 2026 #China #International #Petrochemical #Technology and #Equipment #Exhibition from June 9 to 11, 2026, at #Shanghai New International #Expo #Center. As a #leading petrochemical technology #trade #fair in China, it serves as a #B2B #business #platform for the petrochemical, chemical #processing, refining, and #industrial equipment sectors. #Event brings together #suppliers, engineers, plant operators, and procurement professionals across the #valuechain. https://cnbusinessforum.com/event/2026-china-international-petrochemical-technology-and-equipment-exhibition/
I still want an Apple Vision Air but would understand it being low priority
A report a year ago said that we could expect an Apple Vision Air product in the second half of 2027. This was expected to address both of the issues that have led to the Vision Pro being such a niche product. This week…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Los sistemas de IA generativa NO son artistas. En primer lugar, establezcamos que el arte es una tarea exclusivamente humana.
La IA generativa:
• NO crea
• NO sueña
• NO imagina
• NO se inspira
Los sistemas de IA generativa:
• NO sienten
• NO sufren
• NO subliman
• ¡NO SON HUMANOS!
#AI #genAI #generativeAI #art #artist #artwork #tech #technology #humanrights #inspiration #artists #creative #creation
iPhone 18 Pro Max may not be thicker after all
Late last year a leaker suggested that the trend of the Pro model iPhones getting thicker would continue with the iPhone 18 Pro Max. However, a new report today gives the thickness as 8.75mm, which is exactly the same a…
https://9to5mac.com/2026/06/04/iphone-18-pro-max-may-not-be-thicker-after-all/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
What have we learned from the cybersecurity realm? Hacking is woven into almost every major story of 2026. Halfway through the year, @Techcrunch unpacks an “already horrendous year of digital attacks and hybrid warfare” and looks at the worst hacks and breaches so far:
Report details Apple’s plan to use Nvidia chips for the Gemini-powered Siri
A new report from The Information shares fresh details on how the new Gemini-powered Siri will work under the hood. Here are the details. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Apple kicks off new ‘Privacy on iPhone’ campaign promoting Safari [Video]
Apple is kicking off a new advertising campaign today, highlighting its Safari browser. In particular, the campaign focuses on Safari’s privacy-focused features and how it “keeps data trackers off your back.” more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
New iPads will launch later this year, here’s what rumors say is coming
We’re heading into a summer of software unveilings, but Apple has 15+ new hardware products rumored to launch later in the year—including multiple iPads. Here’s the latest on new iPads to expect. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Apple says Texas App Store age assurance rules start tomorrow after court ruling
Starting tomorrow, June 4, app developers will have to comply with several App Store age assurance requirements tied to new Apple Accounts in Texas. Here are the details. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Apple TV unveils new Anya Taylor-Joy series about a massive heist gone wrong
Next month Apple TV will premiere Lucky, a new original series starring Anya Taylor-Joy. The full trailer for Lucky just dropped, and it looks promising. more…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #9to5Mac [9to5Mac]
Anker 3-in-1 Wireless Charging Station Now $40 Off Ahead of Amazon Prime Day
Amazon is set to host its annual Prime Day event later in June, but you can already find massive discounts across popular accessories right now. This includes year's best prices on Anker chargers, Samsung monitors, Sono…
https://www.macrumors.com/2026/06/07/ankers-prime-chargers-low/
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #MacRumors [MacRumors]
Minecraft Dungeons 2 gets a September release date
Minecraft Dungeons 2, a sequel to Microsoft's dungeon crawler spinoff Minecraft Dungeons, will be released on September 29th. The company originally revealed the game in a brief trailer in March, promising a fall 2026 r…
https://www.theverge.com/games/939551/minecraft-dungeons-ii-2-release-date-trailer
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]



![[?]](https://media.freerobuxextremist.com/media/e6/72/73/e672737b507c0f806d2f46edbecc9be091988fd6c78cb10f7d290184182027b8.png)