Search results for tag #selfhosting
Linux CVE drops. CVE-2026-23111 — nf_tables UAF → root + container escape. A use-after-free in netfilter's nft_map_catchall_activate(). A local unprivileged user gets root, and because it runs through user namespaces, an unprivileged Podman container can break out to the host. A full working exploit dropped June 8, confirmed on Debian defaults.
CVE-2026-46316 "ITScape" It's a KVM/arm64-only guest-to-host escape (vGIC-ITS interrupt emulation). x86 is explicitly unaffected.
CVE-2026-42945 "NGINX Rift" A heap overflow in ngx_http_rewrite_module, CVSS 9.2, getting exploited in the wild.
My main server now has two #Toshiba hard drives. I have no idea why they are so unpopular in the #selfhosting community when they are cheap, quiet, and reliable. I suppose #WD and #Seagate have good marketing departments.
@homelab OK, after playing around a tiny bit, it seems that the code for this exists in #KaniDM
- https://github.com/kanidm/kanidm/pull/2968
- https://github.com/kanidm/kanidm/pull/3535/
but what doesn't exist is ability to reach it and set that up for a user. Oh well.
Blog update:
https://blog.hofstede.it now loads zero external resources. Fonts and Bootstrap are self-hosted, the requests to Google Fonts and jsdelivr are gone. All visits stays between the visitors browser and my server.
Also new:
- Full-text search (Pagefind: fully static, no search backend, no tracking)
- Series navigation for multi-part articles
- Older/newer article links
- A proper 404 page
Static sites don't need third parties.
Blog update:
https://blog.hofstede.it now loads zero external resources. Fonts and Bootstrap are self-hosted, the requests to Google Fonts and jsdelivr are gone. Your visit stays between the visitors browser and my server.
Also new:
- Full-text search (Pagefind: fully static, no search backend, no tracking)
- Series navigation for multi-part articles
- Older/newer article links
- A proper 404 page
Static sites don't need third parties.
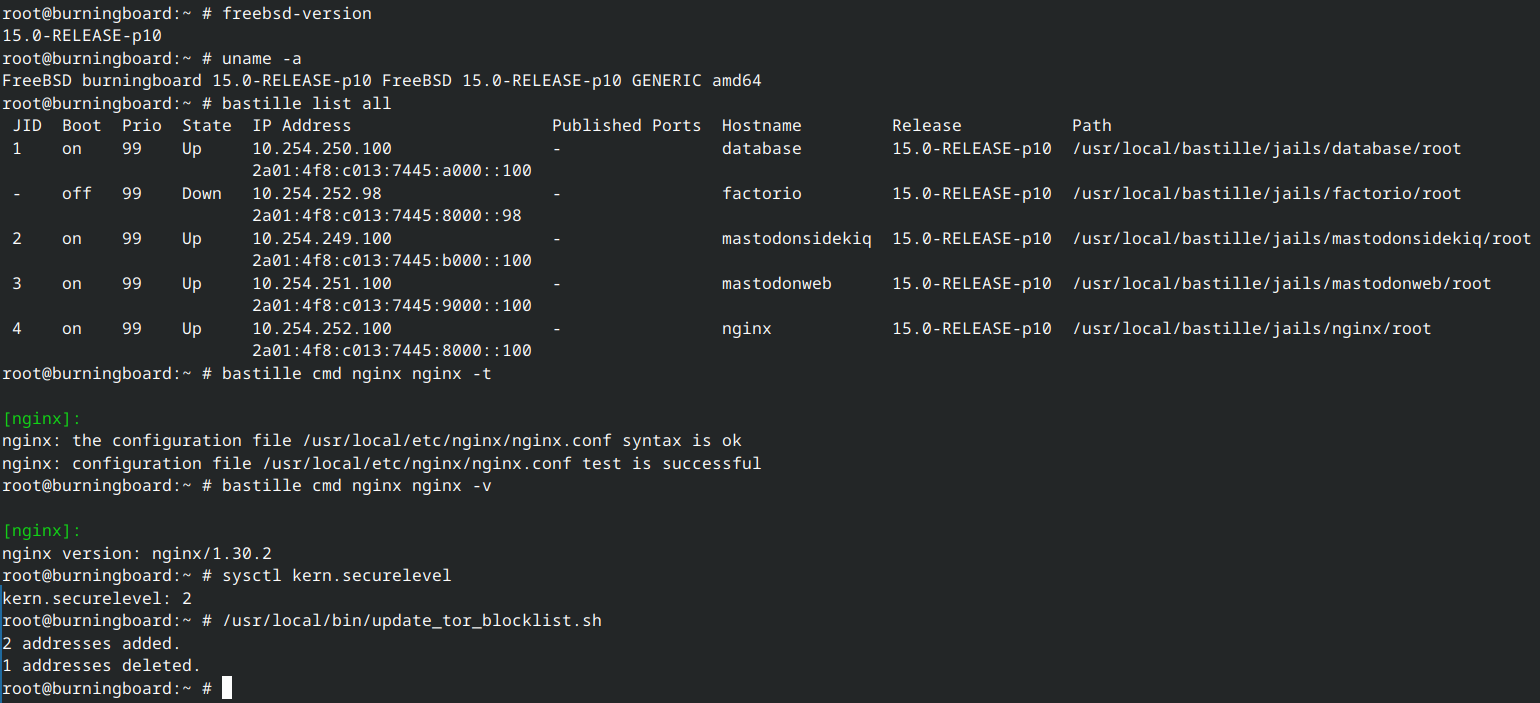
Database cleanup work:
$ psql -c "SELECT pg_size_pretty(pg_database_size('mastodon'))"
pg_size_pretty
----------------
38 GB
(1 row)
$ pg_repack mastodon
INFO: repacking table "public.account_aliases"
....
$ psql -c "SELECT pg_size_pretty(pg_database_size('mastodon'))"
pg_size_pretty
----------------
32 GB
(1 row)
Nice :-) Another successful maintanance ! Also patched up the entire machine and all jails to FreeBSD 15.0-RELEASE-p10 and verified our backups work and are restorable.
@mgfp_fediprofile
https://hub.vocalcat.com/mgfp_fediprofile
After a few attempts in the past, I finally created a FediProfile. I won't be needing Biolink anymore :D.
1/2
#Fediverse #ActivityPub #Linkinbio #OpenSource #SelfHosting #FediProfile #Federation #Federated #FederatedSocialWeb
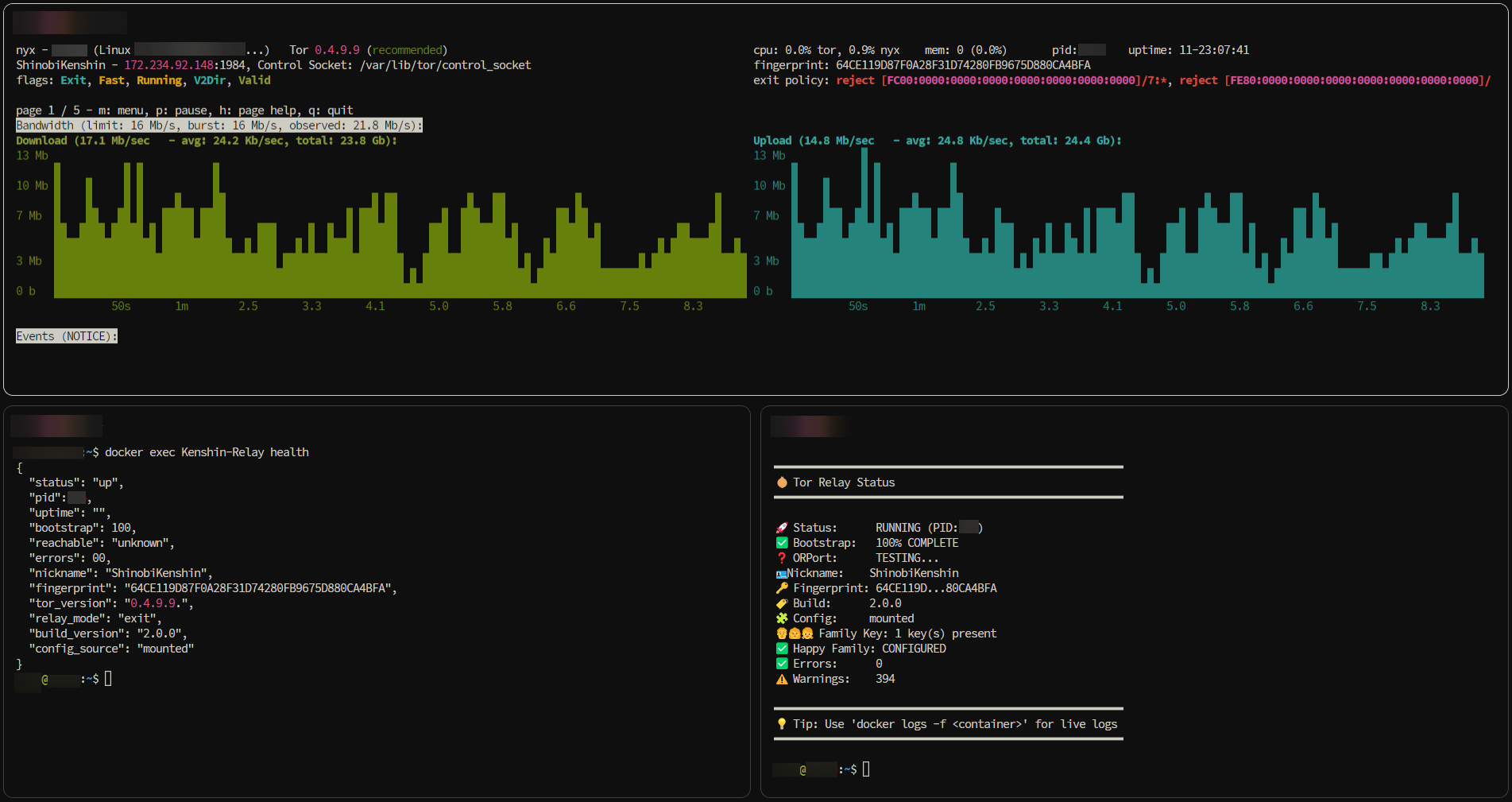
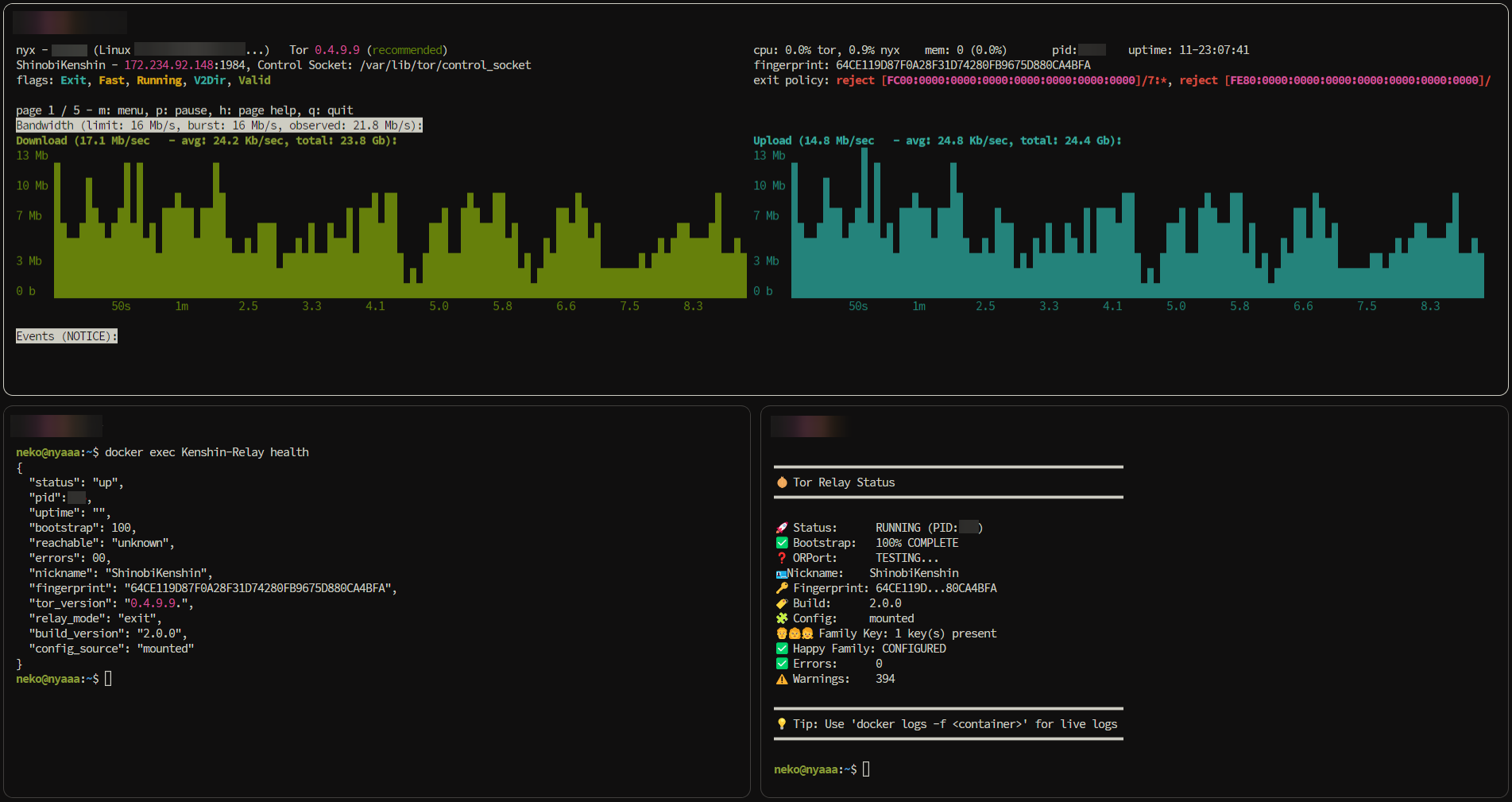
 onion-relay v2.0.0 is out, and it's been a long road from v0.0.1 ⬇️
onion-relay v2.0.0 is out, and it's been a long road from v0.0.1 ⬇️
ℹ️ What started as "one command to run a relay" is now a hardened, production-tested AIO stack: guard, exit, and bridge (obfs4) in a 16.8 MB image.
What's new in v2.0.0:
🩺 health + status tools now expose build_version & config_source
⚡ healthcheck.sh fails fast on missing/empty torrc
🔒 DirPort now defaults to 0 (disabled) in ENV-generated configs
What the project has grown into since launch:
🔑 Happy Family support (Tor 0.4.9+ FamilyId, 🪦 RIP MyFamily lists)
🧰 6 busybox only diagnostic tools
🌍 Battle-tested across 10+ countries: https://relays.brokenbotnet.com
🔐 35+ security fixes, CVE coverage, weekly automated rebuilds
🐋 Works with Docker CLI, Compose, Cosmos Cloud & Portainer
 https://github.com/r3bo0tbx1/tor-guard-relay
https://github.com/r3bo0tbx1/tor-guard-relay
If you care about privacy infrastructure:
🥢 Try it out
🐛 Report bugs
💡 Suggest features
⭐ Star it to help others find it
 Still maintaining this in my free time, donation info
Still maintaining this in my free time, donation info
in the README. And please support @torproject
@eff and @privacyguides too.
Protecting privacy, one relay at a time  ✨
✨
#Tor #Privacy #OpenSource #Docker #FOSS #SelfHosting #Infosec
 v2.0.0 is out, and it's been a long road from v0.0.1 ⬇️
v2.0.0 is out, and it's been a long road from v0.0.1 ⬇️
ℹ️ What started as "one command to run a relay" is now a
hardened, production-tested AIO stack: guard, exit, and
bridge (obfs4) in a 17 MB image.
What's new in v2.0.0:
🩺 health + status tools now expose build_version & config_source
⚡ healthcheck.sh fails fast on missing/empty torrc
🔒 DirPort now defaults to 0 (disabled) in ENV-generated configs
What the project has grown into since launch:
🔑 Happy Family support (Tor 0.4.9+ FamilyId, RIP MyFamily lists)
🧰 6 busybox only diagnostic tools
🌍 Battle-tested across 10+ countries: https://relays.brokenbotnet.com
🔐 35+ security fixes, CVE coverage, weekly automated rebuilds
📦 Works with Docker CLI, Compose, Cosmos Cloud & Portainer
 https://github.com/r3bo0tbx1/tor-guard-relay
https://github.com/r3bo0tbx1/tor-guard-relay
If you care about privacy infrastructure:
🥢 Try it out
🐛 Report bugs
💡 Suggest features
⭐ Star it to help others find it
 Still maintaining this in my free time, donation info
Still maintaining this in my free time, donation info
in the README. And please support @torproject
@eff and @privacyguides too.
Protecting privacy, one relay at a time  ✨
✨
#Tor #Privacy #OpenSource #Docker #FOSS #SelfHosting #Infosec
If anyone was wanting a way out from #Discord, and other similar closed-source forums, #Flarum will soon be having their 2.0 release. rc3 just came out. They have good developer and bugfixing momentum right now. If you have Sysadmin skills, and know of an #OpenSource community in need of a new and suitable OpenSource forum, maybe warm up a VPS, and/or register a domain? And perhaps try out their RC on a testing rig first.
Now is a good time to get into flarum, I say. I've been watching them for a long time, and have done multiple #Debian installs myself.
Note: Flarum doesn't do team voice chat, unlike Discord. But it's a great web forum, with good mobile support (unlike #PHPBB) . Is also lightweight (unlike #Discourse) - can be run on a cheap VPS or Raspberry Pi.
Flarum's 2.0 RC3 announcement:
https://discuss.flarum.org/d/39406-flarum-200-rc3-released-built-by-the-community-almost-ready-for-everyone
Murphys Law mal wieder.
Das neue Nextcloud Update "mal eben" ohne (Datenbank) Backup einspielen, weil hat ja die elf-trillionen male vorher auch ohne irgendwelche Probleme immer funktioniert, wird schief gehen (mit einem Datenbankfehler)
`Foreign key name for table "oc_mail_accounts" collides with the constraint on table oc_mail_accounts.`
Ein Glück nutz ich die NC Mail App nicht, somit tut ein mutiges `drop table` den Dienst.
@peanutsguy @mosu @dlemper Thanks for all your recommendations. I tried #dockhand first, and its “all compose files should be on the main machine” approach didn’t fit my existing infrastructure. Existing stacks adoption will be too much of an issue.
Also #komodo feels much more stable and feature complete compared to #dockhand and especially to #arcane. Not the simplest tool but pretty intuitive after some time of tinkering.
#docker #homelab #SelfHosted #selfhosting #selfhost
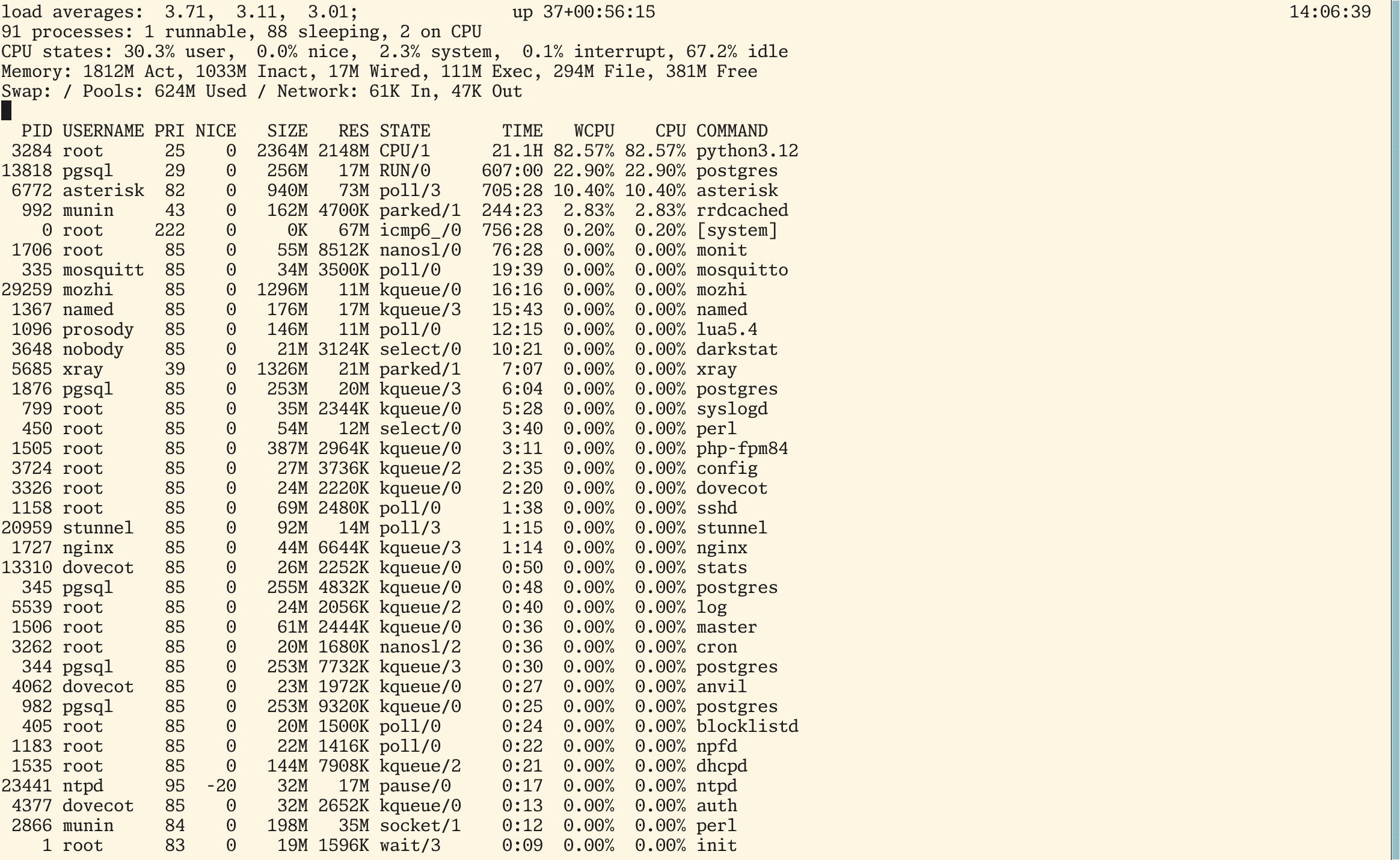
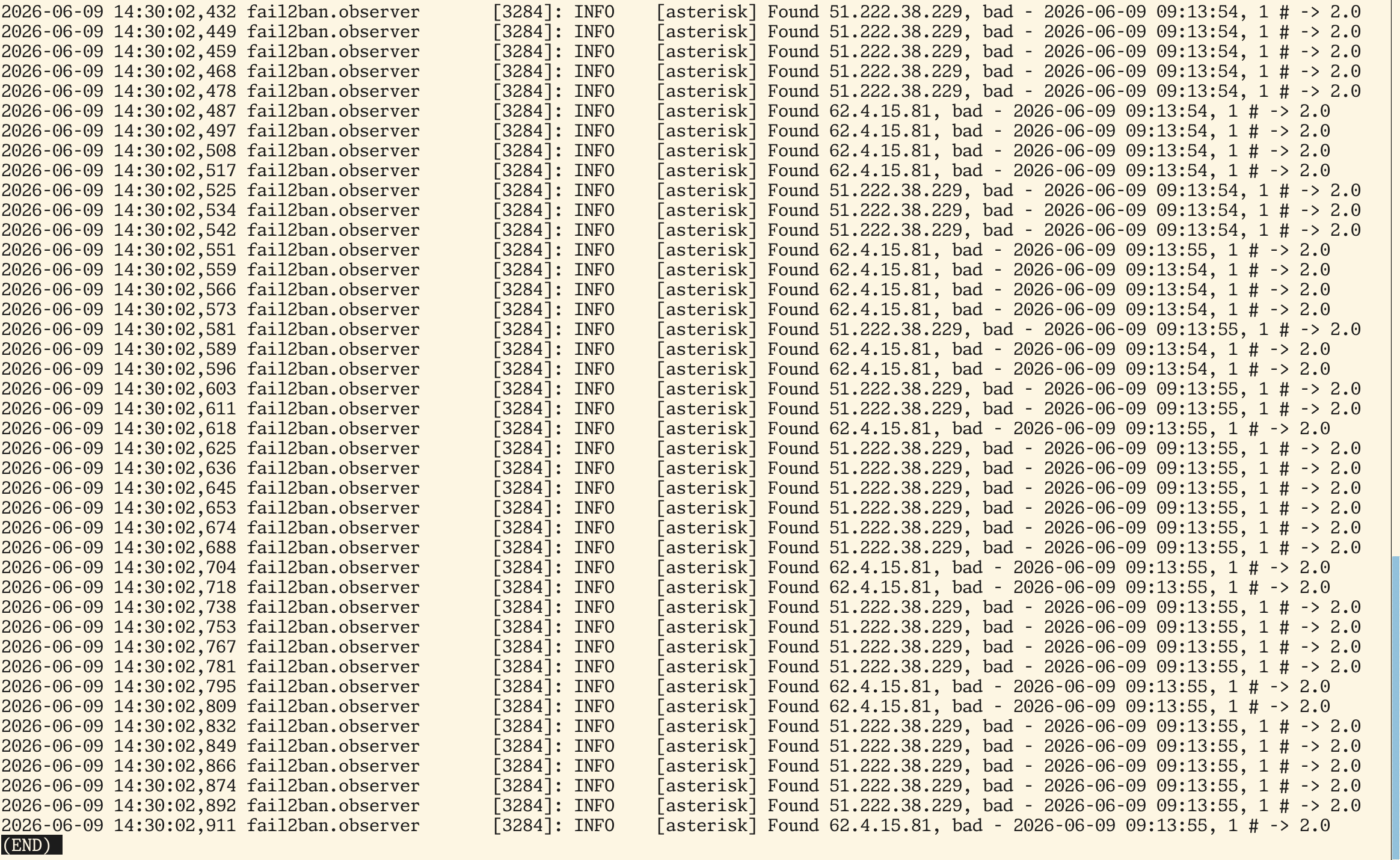
Oh fuck, I was mistaken — it was a real attack, not LLM bots  — someone, using machines from French hosting, was trying to connect to my Asterisk box, using various SIP endpoints.
— someone, using machines from French hosting, was trying to connect to my Asterisk box, using various SIP endpoints.
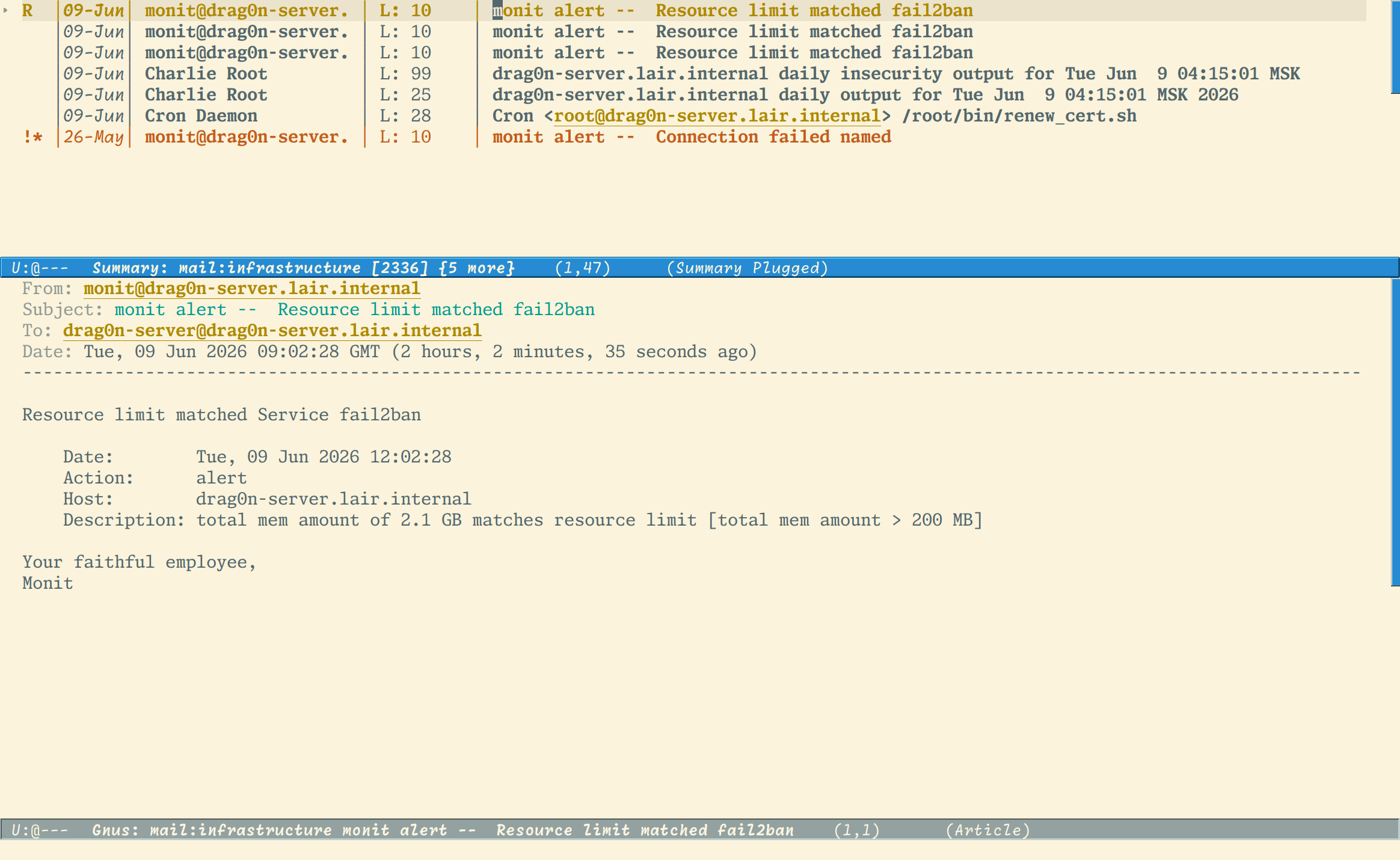
The attack was started at Monday's night and was found only because monit reported about too much memory eaten by fail2ban 
Interesting, why fail2ban didn't banned attacker's IP, because it should do that right after failed attempt to login?  Tine to revisit fail2ban jails configs…
Tine to revisit fail2ban jails configs… 
I think one of the coolest things about #Mastodon is all the small-time instances. It proves there are tons and tons of people out there who get how to do self-hosting. They get DNS, domain registry, and some System Administration skills, to empower themselves, and make a stand on the #internet, participating in a federation whatsoever.
Email doesn't really enjoy this same status: it's sort of (effectively) "semi-federated". Even after doing all the correct DNS vodoo (SPF, DKIM, DMARC), one might be cursed anyway, because one's IP address comes from some disreputable IP block. This "original sin" can't really be cleansed, according to #Google , #Microsoft, etc, who silently and ruthlessly can send all one's incoming, self-hosted email messages to the recipient's spam folder.
Ok #Arcane is no longer a simple #Docker orchestrator for #HomeLab. Also, their v2 migration guide is a good example of bad documentation.
Anything except #UptimeKuma? Any recommendations?
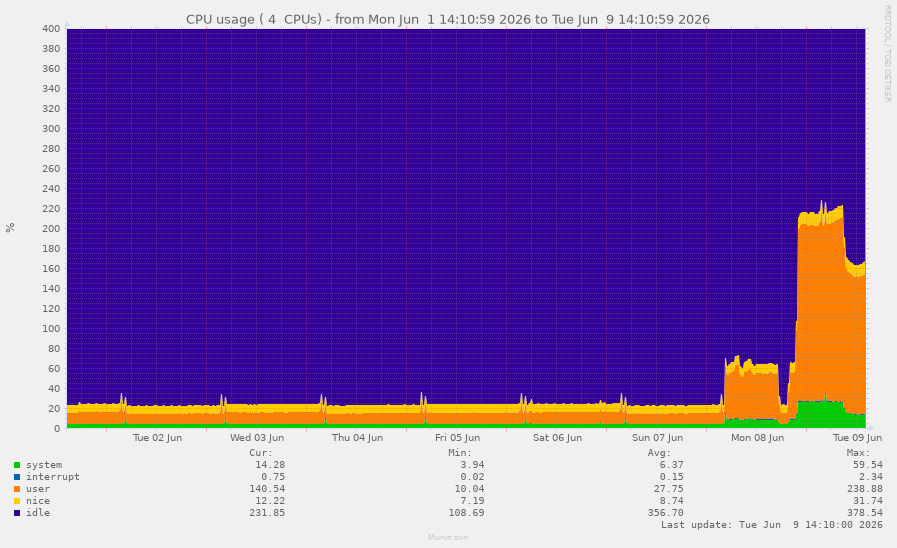
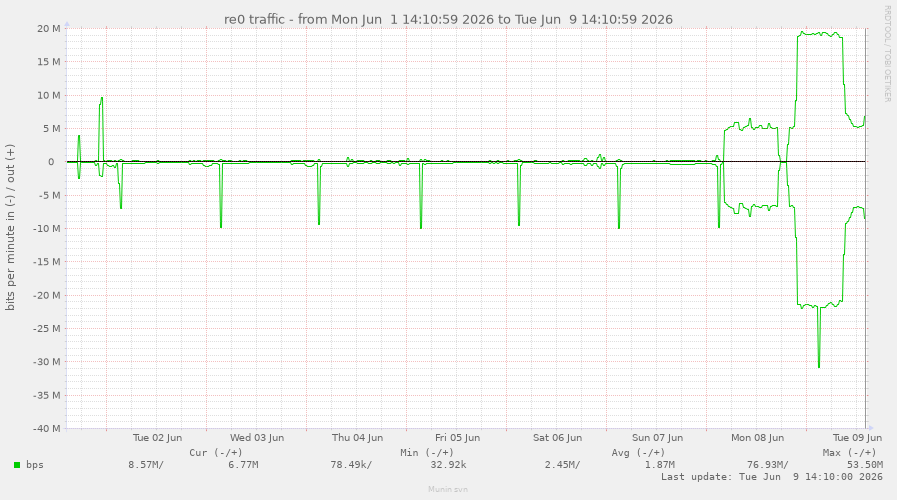
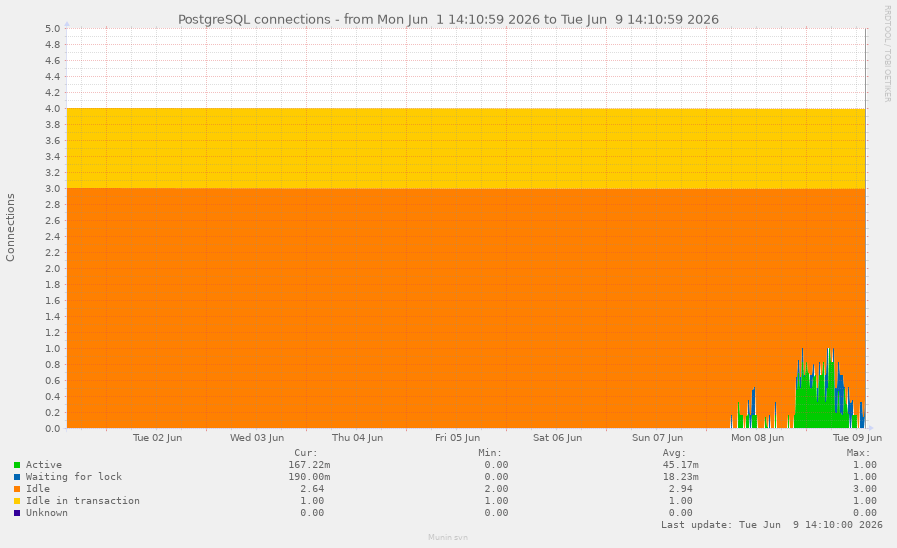
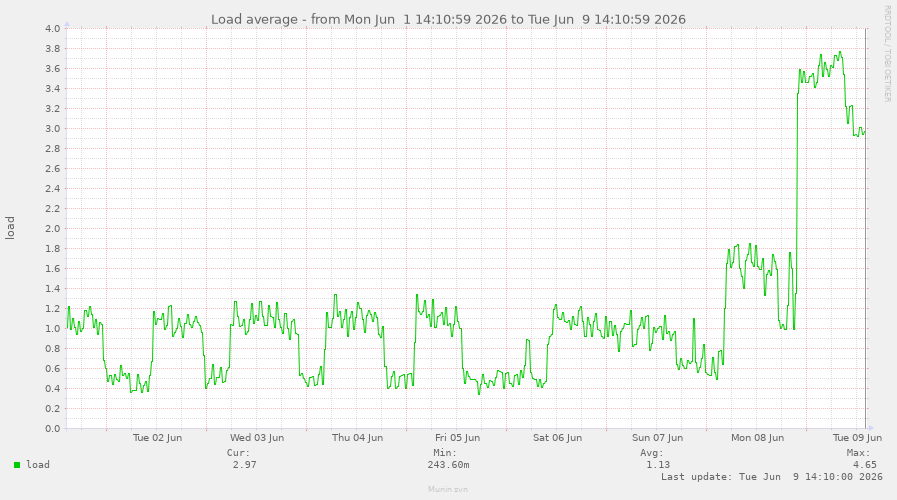
Some graphs  from #Munin with LLM-bots attacking my kitchen server.
from #Munin with LLM-bots attacking my kitchen server.
Graphs spans to the whole week, so on the left there is a normal state of my server. And on the right — attack is happening.
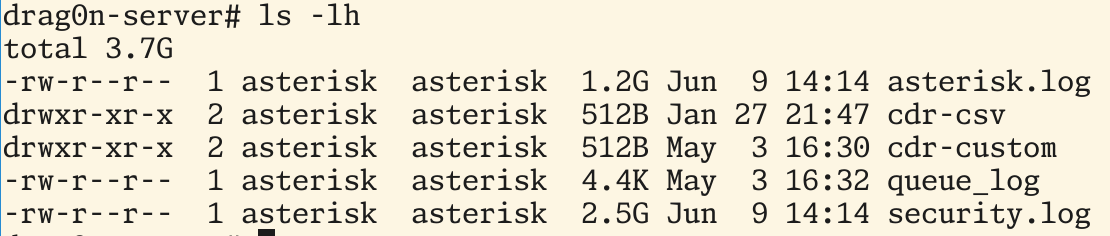
Then, I logged into my box and found that fail2ban, Asterisk and PostgreSQL aren't feeling well. The system load and the traffic amounts was unusual — the parameters are completely differs from which I used to see since server installation.
I checked fail2ban logs and found that it is still parses the data from Asterisk log which were happen at near 5 hours ago  And there were total mess in the Asterisk security.log (see screenshot) — some dumb (as it programmers
And there were total mess in the Asterisk security.log (see screenshot) — some dumb (as it programmers  ) LLM-bots were constantly trying to connect to my Asterisk server with HTTP protocol, evaluating it as a web-server, I dunno
) LLM-bots were constantly trying to connect to my Asterisk server with HTTP protocol, evaluating it as a web-server, I dunno 
And the Asterisk logs became enormously big — while newsyslogd wasn't invoked — they eat at near 4 GB  . I didn't specify the maximal size of Asterisk logfiles in the /etc/newsyslog.conf, because I wasn't expected a lot of lines in the PBX logs, which is in use only for my relatives.
. I didn't specify the maximal size of Asterisk logfiles in the /etc/newsyslog.conf, because I wasn't expected a lot of lines in the PBX logs, which is in use only for my relatives.
Le guide IPv6 (#OVH / #NPM / #Proxmox / #Docker) fait peau neuve !
Vous connaissez déjà cette page de mon wiki, mais elle vient de s'offrir une réécriture complète !
Pourquoi ? Pour couvrir proprement deux cas de figure bien distincts selon vos besoins. Que vous soyez dans une config ou dans l'autre, tout y est détaillé pas à pas.
👉 À checker et à mettre dans vos favoris ici : https://wiki.blablalinux.be/fr/deploiement-ipv6-ovh-npm-proxmox-docker
Bonne lecture et bon déploiement !
Huh, looks like the new ASes, with LLM-bots attacking servers, just dropped 
TLDR: there are AS12876 and AS16276 — both located in France (Scaleway SAS and OVH SAS). My Asterisk self-hosted box was attacked from the next IPs: 62.4.15.81 and 51.222.38.229.
Today, after I was checked my e-mail, I found three warnings from Monit about fail2ban exhausting limits in my small server in the kitchen (Intel Atom N2800 1866 MHz and 4 Gb of RAM). First e-mail warns about fail2ban ate 200 MB of RAM, next about 500 MB of RAM and the last e-mail warns me that fail2ban ate 2 GB of RAM 
🚛 Neuer Beitrag auf ChristiansBlog.eu
Nextcloud-Server von einer USB-NVMe auf eine interne SATA-Festplatte migrieren – ohne Neuinstallation
Ein Praxis-Tutorial zur Migration eines laufenden Debian- und Nextcloud-Servers von einer USB-NVMe auf eine interne SATA-Festplatte – inklusive GRUB, rsync, fstab und typischer Fehlerfallen.
🔗 https://christiansblog.eu/post/tutorial/serverumzug/
#NextCloud #Debian #Linux #Server #Migration #NVMe #SATA #Apache #GRUB #Tutorial #HomeServer #Selfhosting
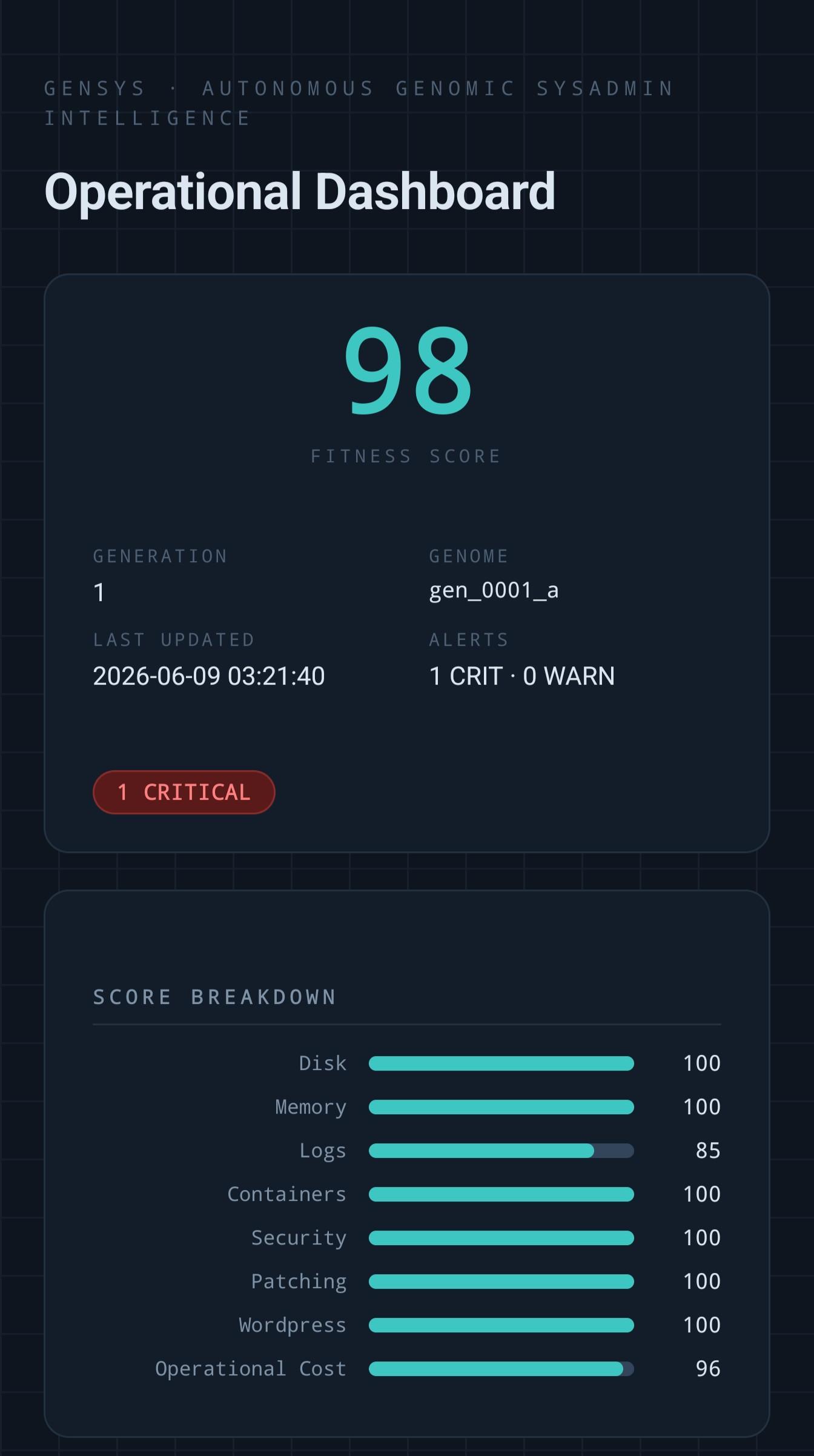
I have totally re-engineered the Genomic Sysadmin tool. Emphasis is on generating standalone code vs Ai centric processing, with universal Ai stubs that can run off cloud or local models with a fallback to deterministic evaluators.
Added emphasis on pressure sensitive governance.
Eg. If the firewall is getting more hits, the security posture is elevated, if diskspace, housekeeping...etc
Second major "innovation", the mission.md is actually composing the codebase as the compute windows flap.
It's currently just a simplified version of my existing blog, but I'm hosting this website on my Raspberry Pi Zero for testing purposes:
We will see how things go over time, then possible port over the "real" thing 😛
New post: IPv6 Foundations.
IPv6 isn't "the future of the internet." It's the internet. IPv4 is the relic we keep alive on NAT life support.
A laid-back tour through the basics: how the addresses are built, the two rules for crushing out the zeros, a /64 per subnet so you stop counting hosts, SLAAC, and why blocking ICMPv6 is a self-inflicted wound.
And no, dual-stack isn't a destination. It's a burden.
https://blog.hofstede.it/ipv6-foundations-the-internet-protocol-you-should-already-be-using/
Also, I didn't get the notification about high server temperature from #Beszel because of this: https://github.com/henrygd/beszel/issues/2042 (still not released).
So the federation is working on my #Wanderer instance, and you can actually follow me there from any #ActivityPub instance: @yehor@wanderer.glitchy.social
The issue was actually in my #Mastodon instance: https://mastodon.glitchy.social/@yehor/116713584141417614
#Fediverse #homelab #selfhosted #selfhosting #selfhost
AodeRelay boostedWrote my first server announcement. Because yesterday, after updating my #Mastodon instance to 4.5.11, I didn't realise the Sidekiq died.
I spotted an unusual server load and temperature 24 hours later, found out that it was a Mastodon LXC, and realised there had been nothing processed by Sidekiq for 24 hours already.
I'm not sure about the reasons, because I didn't find anything useful in the logs. I definitely need better monitoring for #GlitchySocial.
Also wrote a guide on setting up #Wanderer instance bare-metal using #systemd service: https://github.com/open-wanderer/wanderer/discussions/817#discussioncomment-17209054
Halp! I just installed Yunohost on my home server with a wired connection.
Access to my apps works fine on devices with ethernet cable. But my wireless devices can only access my admin page, not the app portal.
Is this a common issue?
I think #SelfHosting is an important skill to learn, for anyone with the aptitude for it. I think the internet can't really be made a better place, until people learn to use those same skills to "staple the internet to real life". Like start from a place in one's real-world existence and look around. There are real-world organizations, and various community groups.
These groups should ideally roll their own self-hosted services: forums, group chats, file-sharing, etc. That's what I mean by "stapling": real world regional orgs aligning to the services they self-host. It's the opposite of using Big Tech forums: the Facebooks, Instagrams, etc of the world, where the platforms can't be trusted, and are totally certain to enshittify. In this way, #DataSovereignty is gained.
Yes, people will need a password manager to manage all those passwords. Or perhaps regional SSO servers - run by a city of province/state - can unify these accounts somewhat. Password management and backing up the password database (eg. .kdbx file) should be taught in school.
People actually visiting over coffee/tea (or meals), are the right time to help someone less technically inclined (in person) to install a new #OpenSource friendly app, like Signal or #DeltaChat
Yes, it won't be easy, *but I don't see an alternative*. There's pretty much no escape from the Tech Bro billionaires otherwise.
✨ Demain 18h : rendez-vous mail !
Abonnés à la campagne Wiki, attendez-vous à recevoir demain une belle dose de contenu technique pour vos serveurs. Soyez prêts ! 📖
#BlablaLinux #Wiki #Tips #SelfHosting
MATRIX-Bridges sind der absolute Messenging-Game-Changer! part 3 #did
Hol dir die volle Kontrolle über deine Kommunikation zurück! 🚀
In diesem dritten Teil meiner Matrix-Serie zeige ich dir, wie du mit sogenannten Bridges die Brücke zu WhatsApp, Telegram, Discord und sogar Instagram schlägst. Wir bündeln alles in einer einzigen, sicheren Open-Source-Oberfläche: Element. Das macht nicht nur euch, sondern auch euren Kontakten den Umstieg umso einfacher. Denn wir müssen ganz dringend raus aus diesen goldenen Käfigen.
Ich nehme dich mit durch meinen Prozess, zeige dir die Stolpersteine bei der Konfiguration (Docker, Config-Dateien & Co.) und wie du die Bridges für die gängigsten Messenger erfolgreich aufsetzt. Außerdem erfährst du, warum Selfhosting für mich nicht nur ein Hobby, sondern eine Philosophie für digitale Souveränität und Privatsphäre ist.
Du hast auch lieber "ADMIN-RECHTE statt RECHTE ADMINS" ?
Hier gib's die Fashion zum Statement:
https://lex-takuna.myspreadshop.de
In diesem Video siehst du:
00:00 - Intro: Austausch über Matrix & Community-Feedback
01:00 - Was sind Matrix-Bridges? (WhatsApp, Discord, Telegram, Instagram)
02:02 - Das Problem: Konfiguration klappt nicht „Out of the Box“
03:18 - Speedrun: Matrix-Stack neu aufsetzen & Installation
04:18 - WhatsApp-Bridge konfigurieren (Config & Registration YAML)
06:40 - Wichtiger Fix: Synapse Neustart & Token-Abgleich
07:44 - Hookshot: Ausblick
08:21 - WhatsApp Login & Kontakte/Gruppen synchronisieren
10:00 - Pro-Tipp: WhatsApp-Status-Benachrichtigungen deaktivieren
11:39 - Telegram-Bridge: Login via Telefonnummer
12:34 - Discord-Bridge: Server (Guilds) & Channels einbinden
14:54 - Instagram-Bridge: Login via Cookies/CURL (DevTools)
16:13 - Fazit: Warum Selfhosting & digitale Souveränität wichtig sind
17:48 - Kleiner Merch-Drop: "Adminrechte statt rechte Admins"
18:50 - Outro & Ausblick auf PeerTube / Fediverse
Peertube: https://makertube.net/c/lex_takuna/videos
Mastodon: https://burningboard.net/@LexTakuna
Matrix: @lex:trixie.takuna-homelab.de
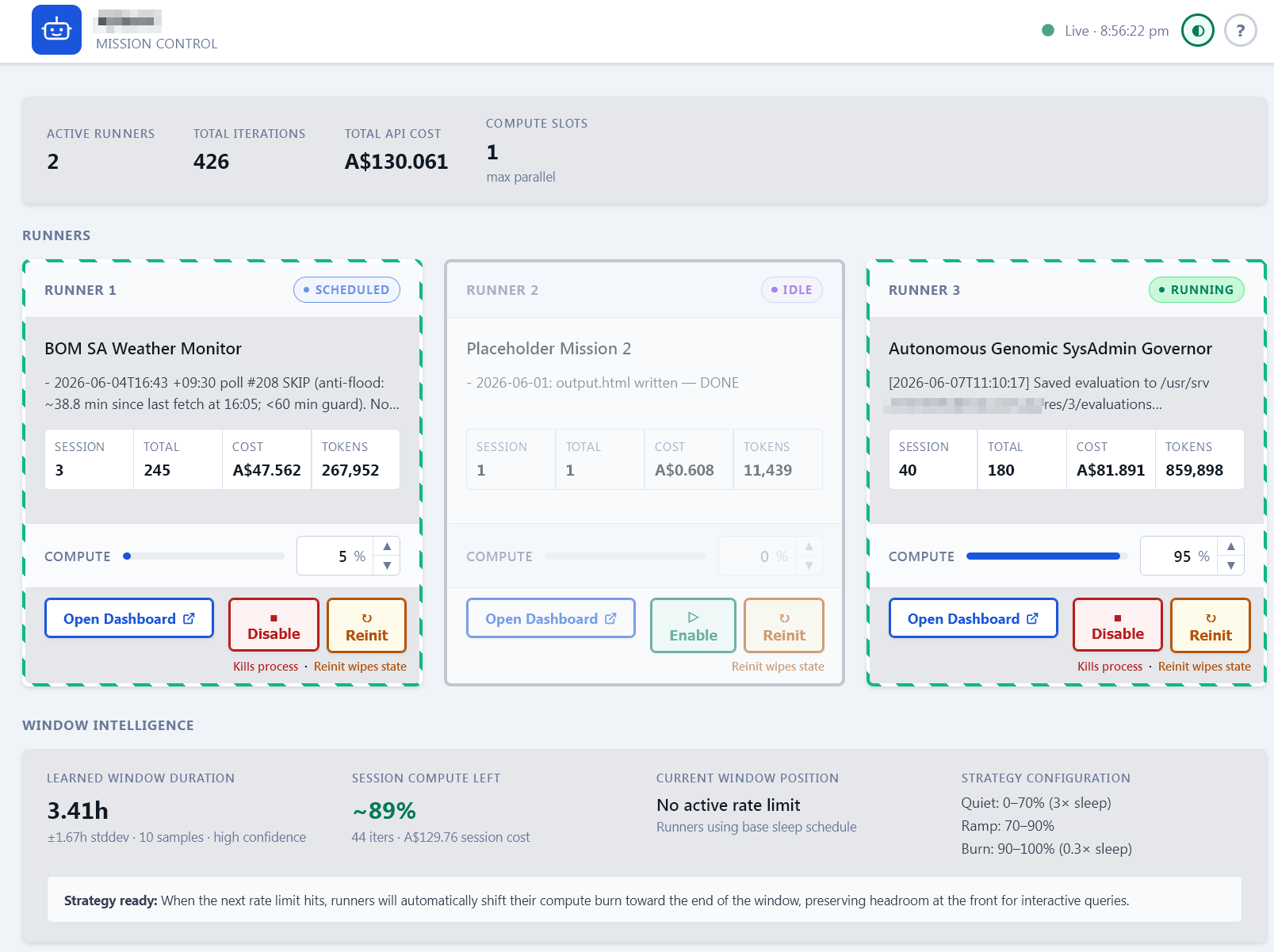
I really should stop fucking with the tool, but there is always one more tweak to make it more functional. Takes a lot of discipline to stop poking at it...
... of which I have none.
This is the current iteration.
3 runners (but you can add as many as you want, just by cloning the runner directory)
Each runner has an autonomous mission.md - this is basically a super prompt. You can see, I can assign the compute load (its 5%, 95% atm).
The load logic was broken and I only picked it up by watching the runners cycle.
A cute little function I added, the ant-trail moves faster the more compute % its got allocated, so you can see at a glance where you are at.
There is a logic that estimates the available compute window and ramps up towards the end, to burn up the remaining compute, while allowing a window at the start, should you need it for manual prompts.
#sysadmin #vibecode #llm (windup) #codemonkey #selfhosting #vps
Die eigene Nextcloud zu betreiben geht einfacher als gedacht. Dank Nextcloud AIO und meinem ausführlichen Video-Tutorial gelingt die Installation auch ohne Vorkenntnisse. Und falls doch Fragen aufkommen sollten, steht unsere Community mit Rat und Tat zur Seite.
https://gnulinux.ch/video-nextcloud-all-in-one-dein-einstieg-ins-selfhosting
So @delta updated itself (fdroid and linux (cachyos)) to 2.51, now call on 1 to 1 is enabled by default.
This version will arrive soon on google playstore and ios / microsoft (depending the update delay on those platform).
#call #endtoend #privacy #sovereinty #decentralization #decentralized #deltachat #security #phone #foss #freedom #selfhosting
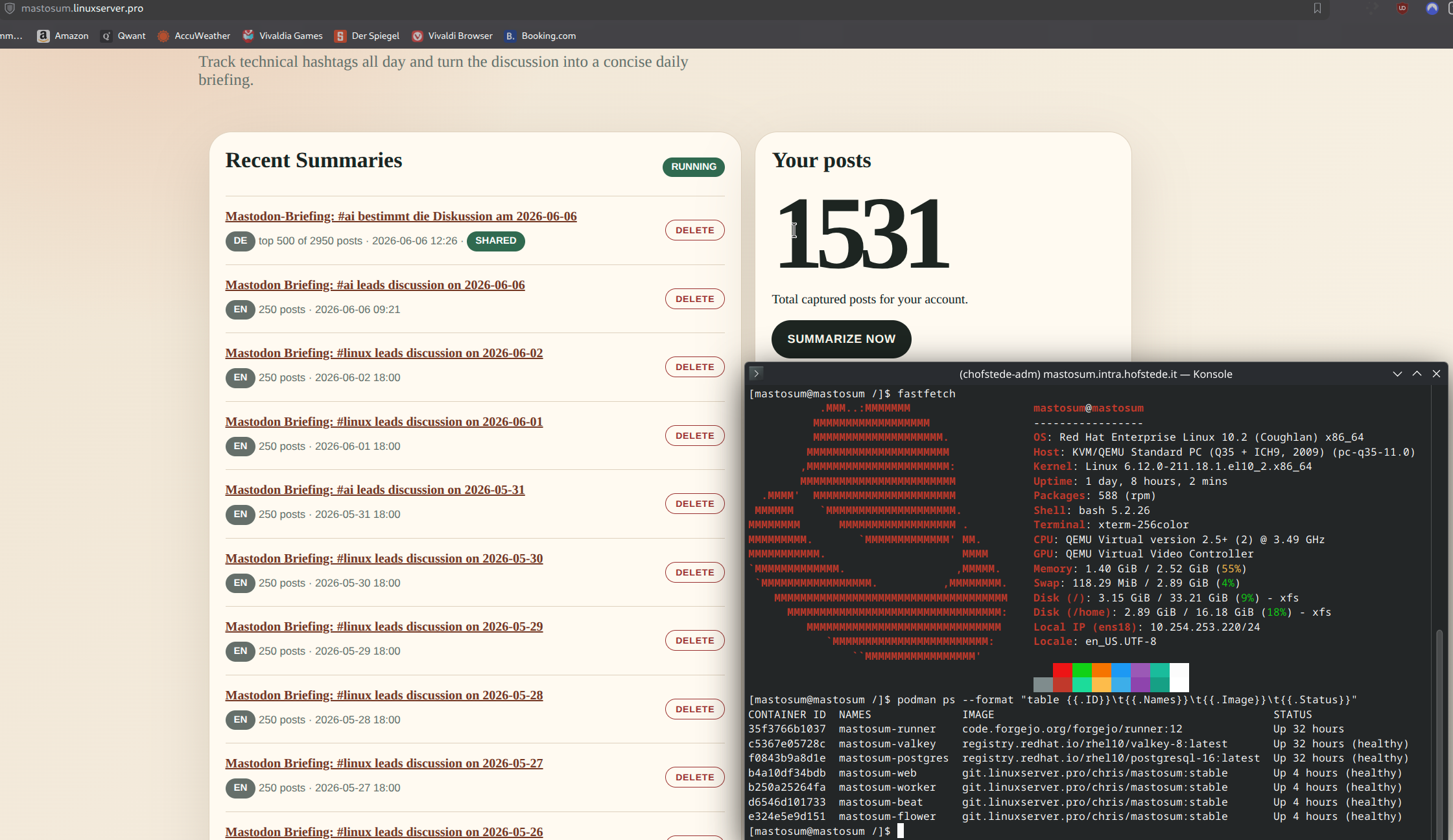
Weekend project that turned into infra I actually run daily: MastoSum.
The stack: RHEL host, 100% rootless Podman. Web on FastAPI, Celery worker/beat/flower, PostgreSQL 16, Valkey. All on userspace networking (pasta), images built & shipped by a self-hosted Forgejo runner. No root daemon, no privileged anything.
What it does: tracks technical hashtags all day and produces one daily briefing, every point linked to the original post + author. It reads only public hashtag timelines, credits every source, and trains on nothing.
And yes, an LLM writes the prose: a local Ministral model from French lab Mistral AI, running on my own hardware. No cloud, nothing leaving the box. Saying that plainly, not burying it. The whole design goal was to point readers *back* at the authors, not replace reading them.
Example output:
https://mastosum.linuxserver.pro/s/OGuLC5whmCS1ET9jAe9leg
MATRIX-Bridges sind der absolute GAME-CHANGER ! part 3 - #did
In diesem dritten Teil meiner Matrix-Serie zeige ich dir, wie du mit sogenannten Bridges die Brücke zu WhatsApp, Telegram, Discord und sogar Instagram schlägst. Schluss mit dem App-Chaos und den "goldenen Käfigen" der Tech-Giganten! Wir bündeln alles in einer einzigen, sicheren Open-Source-Oberfläche: Element. Das macht nicht nur euch, sondern auch euren Kontakten den Umstieg umso einfacher.
Ich nehme dich mit durch meinen Prozess, zeige dir die Stolpersteine bei der Konfiguration (Docker, Config-Dateien & Co.) und wie du die Bridges für die gängigsten Messenger erfolgreich aufsetzt. Außerdem erfährst du, warum Selfhosting für mich nicht nur ein Hobby, sondern eine Philosophie für digitale Souveränität und Privatsphäre ist.
Du willst auch lieber Admin-Rechte als rechte Admins ? Hier gib's die Fashion zum Statement.
https://lex-takuna.myspreadshop.de
In diesem Video siehst du:
00:00 - Intro: Austausch über Matrix & Community-Feedback
01:00 - Was sind Matrix-Bridges? (WhatsApp, Discord, Telegram, Instagram)
02:02 - Das Problem: Konfiguration klappt nicht „Out of the Box“
03:18 - Speedrun: Matrix-Stack neu aufsetzen & Installation
04:18 - WhatsApp-Bridge konfigurieren (Config & Registration YAML)
06:40 - Wichtiger Fix: Synapse Neustart & Token-Abgleich
07:44 - Hookshot: Ausblick auf Home Assistant Anbindung
08:21 - WhatsApp Login & Kontakte/Gruppen synchronisieren
10:00 - Pro-Tipp: WhatsApp-Status-Benachrichtigungen deaktivieren
11:39 - Telegram-Bridge: Login via Telefonnummer
12:34 - Discord-Bridge: Server (Guilds) & Channels einbinden
14:54 - Instagram-Bridge: Login via Cookies/CURL (DevTools)
16:13 - Fazit: Warum Selfhosting & digitale Souveränität wichtig sind
17:48 - Kleiner Merch-Drop: "Adminrechte statt rechte Admins"
18:50 - Outro & Ausblick auf PeerTube / Fediverse
Uh...my Genomic #Sysadmin tool is jibber jabbing at me.
It started creating evolution progress reports.
Its only a couple of days into the 1st epoch.
Honestly, part if the fun is observing all the new artefacts this experiment is producing.
Its got free hand to self mutate for efficacy.
Genome Evolution Assessment
The primordial genome (gen_0001_a) is performing close to optimal given the environmental constraints. The operational_cost dimension score of 70 is structurally fixed by the backup age — genome mutations to operational_cost weights (cpu_cost_weight, memory_cost_weight, admin_attention_cost) cannot reduce the 40-point backup penalty. This creates an evolutionary ceiling for this dimension until the backup is restored. Generation 2 mutations will correctly target operational_cost genes but will achieve minimal fitness gains from this dimension until the backup situation is resolved. Evolution is healthy and functioning as designed.
I seem to have written a mini web firewall. I've been watching my self-hosted blog web server's logs, because I wanted to block AI web bots, and I noticed (again) that I get a lot of malware vulnerability scans. My site is static, so they're unlikely to ever "get in" because they all make requests that result in a 404 Not Found, or other 4xx response, but they annoy me and I needed a small, low intensity project to try to get my brain going again.
So I've come up with a very simple Python script that tails the log, looking for 4xx codes. If it sees a known "bad" request, or too many 404s from an address, it firewalls the IP address, and stops it in its tracks.
I need to make it a bit easier to use, and probably collect a list of failed requests to add to the bad list, but I'm quite pleased with it so far. Obviously I'm not Fortinet but it feels good to fight back in even such a tiny way.
If you want to set up several different online services but can't afford different domain names for them all, you can just use subdomains of one domain instead. They are limitless and cost nothing extra.
e.g. You could have a Mastodon server at social.example.com, a PeerTube server at video.example.com, a Nextcloud server at cloud.example.com etc.
Each subdomain can use totally different software and be on totally different hosting providers.
Der di.day bietet nun auch die Möglichkeit sich als Helfer_in einzutragen. Ihr findet mich hier: https://experts.di.day/experts/17
Tragt euch doch auch ein, damit wir möglichst vielen Menschen helfen können ihr digitales Leben etwas freier und sicherer zu gestalten.
Self-Hosting an ActivityPub Video Podcast Is Surprisingly Affordable
1/
Imagine this.
You want to launch your own video podcast.
A new episode every week.
Each episode is 1 hour long.
Full HD (1080p), 60 fps video.
What would it cost to host it yourself?
Before I ran the numbers, I assumed it would be expensive — maybe even impractical.
I was wrong.
The reality is surprisingly affordable.
Here is why.
...
Funkwhale is a free open music and audio platform for the Fediverse, which has just been updated to version 2.0. Find out more at:
Their account is:
If you want to host your own Funkwhale server without doing any techy stuff, there are managed hosting providers at https://cloud68.co/managed-hosting/funkwhale and https://weingaertner-it.de/index.php/produkt/funkwhale/?lang=en
You can also self-host manually using the instructions at https://docs.funkwhale.audio/administrator/index.html





 [
[
![[?]](https://social.christiansblog.eu/fileserver/01WA01Q4MR8ABFAKNX4SMBND2X/attachment/original/01KRR4FNK4A09JF7AMSTVGNCAE.png)

![[?]](https://gts.tumfatig.net/fileserver/01FJ093H6Y5VGN20G998J7KN1M/attachment/original/01JZTJV1P9RVJ502PCXKN68R1F.jpeg)
 There is no Cloud!
There is no Cloud! Only someone else’s
Only someone else’s 